Identity theft protection services promise peace of mind, but many fall short of their marketing claims. We at Hays Cauley, P.C. have seen countless clients discover gaps in their coverage after fraud strikes.
The truth is that no service alone stops identity theft. You need a layered approach that combines what these services offer with your own active defense strategies.
What Identity Theft Protection Services Actually Monitor
How Credit Monitoring Works
Identity theft protection services operate on three core functions, and understanding what each one genuinely delivers matters far more than the marketing language surrounding them. Credit monitoring remains the primary tool these services offer, scanning the three major bureaus-Equifax, Experian, and TransUnion-for new accounts, inquiries, or changes linked to your Social Security number. According to the FTC Consumer Sentinel Network, 6.47 million identity theft reports landed in 2024, with about 124,000 involving losses of $10,000 or more. Services like Aura and Identity Guard include three-bureau monitoring on most plans, alerting you within days when suspicious activity appears. This matters because new-account fraud represents one of the fastest-growing identity theft categories, and catching it early prevents months of damage.
Credit monitoring has a hard ceiling, though: it only flags activity that appears on credit reports. Financial fraud that doesn’t touch your credit file-like unauthorized bank transfers or wire fraud-sits outside this net entirely.
Dark Web and Data Breach Scanning
Beyond credit reports, these services scan for your personal data circulating on the dark web and in breached databases. Providers market this as comprehensive protection, but the reality is far narrower. Billions of records from past breaches already exist in multiple locations, and no vendor monitors all sources continuously. A WIRED investigation found that dark web monitoring claims are routinely overstated, with services unable to track every forum or marketplace where stolen data surfaces. What actually happens is alerts for your specific information appearing in newly indexed breaches, not prevention of the breach itself.
Recovery Assistance and Insurance Limits
Recovery assistance represents the third pillar-when fraud occurs, some services provide case managers who coordinate with creditors and credit bureaus to restore your accounts. NordProtect and LifeLock advertise white-glove restoration, where the service handles the heavy lifting rather than leaving you to navigate disputes alone. This support carries real value if you actually use it, but the insurance component typically caps reimbursement at modest levels. NordProtect, for example, caps lost wages and care time at $5,000 despite headline coverage of $1,000,000. The gap between advertised protection and actual payout limits catches most consumers off guard during claims.
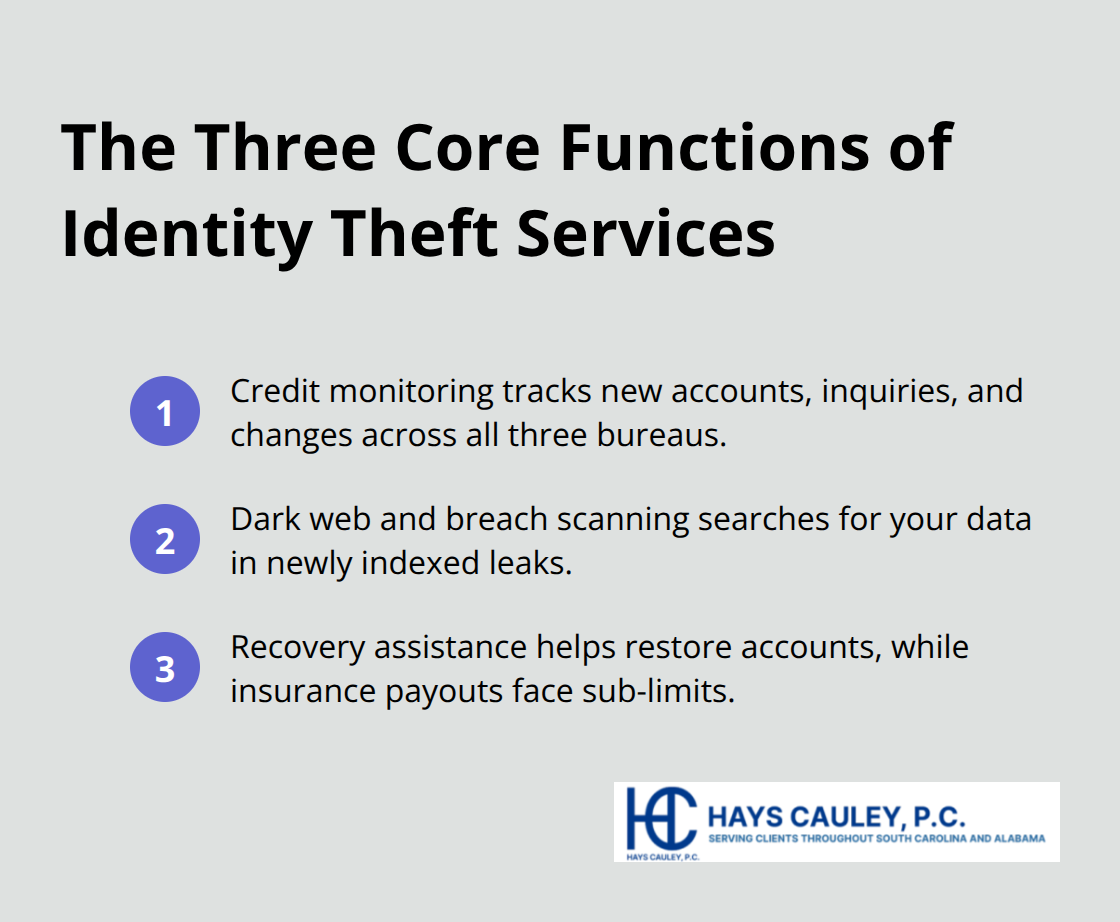
These three functions form the foundation of what protection services deliver, yet each one operates within significant boundaries. Understanding these boundaries becomes essential when you evaluate whether a service fits your actual needs-and what additional protections you must layer on top to close the gaps these services leave behind.
Where Identity Theft Protection Actually Fails
Reactive Detection Instead of Prevention
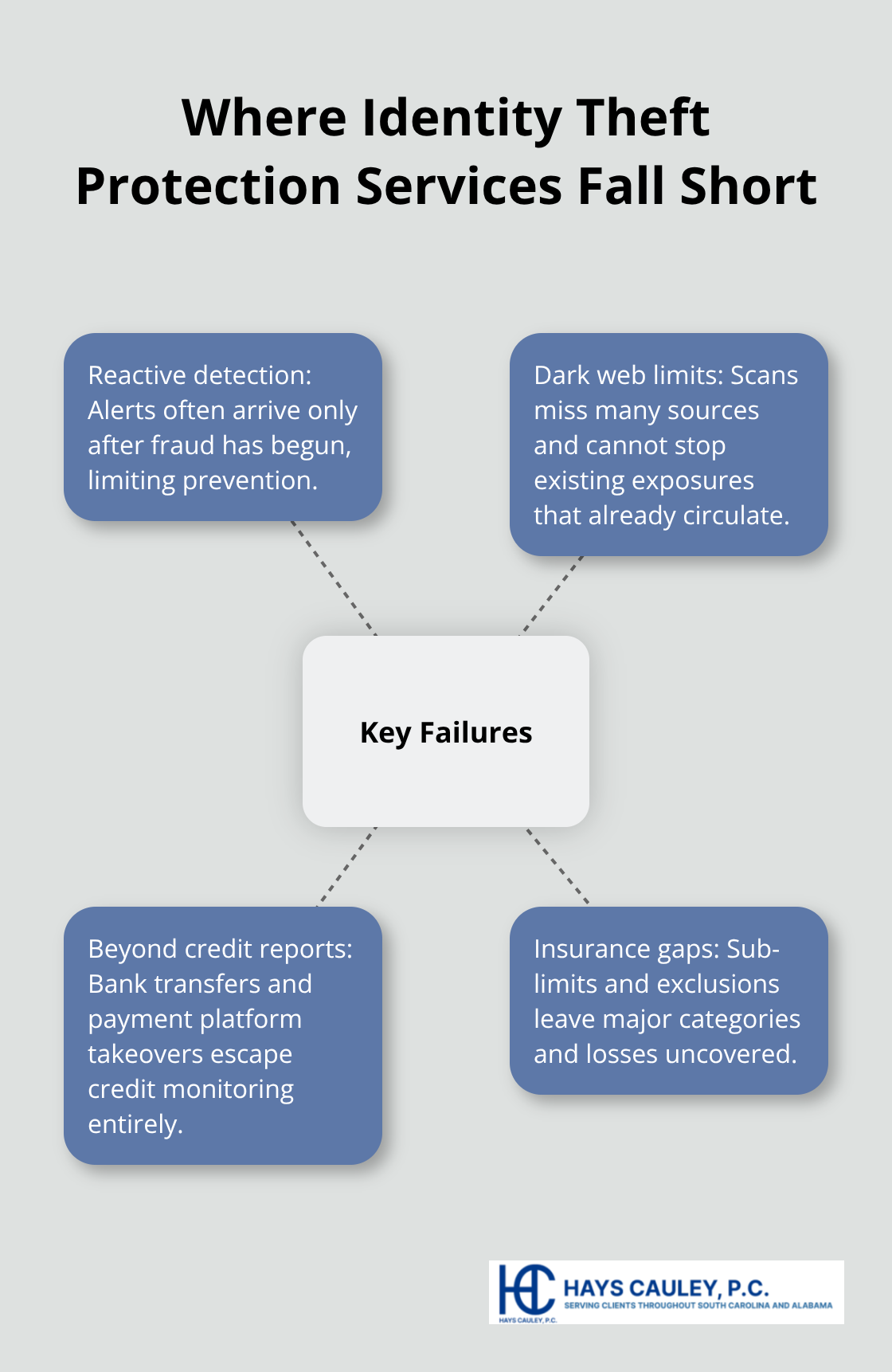
Identity theft protection services operate in a reactive world, responding after damage occurs rather than preventing it. The FTC Consumer Sentinel Network recorded 6.47 million identity theft reports in 2024, yet the services marketed to stop this crime focus almost entirely on detection and recovery, not prevention. This fundamental mismatch between what consumers expect and what services deliver creates dangerous blind spots. Criminals strike first; services alert you afterward.
The Dark Web Monitoring Illusion
Dark web monitoring, despite being advertised as comprehensive, cannot track the billions of records already circulating across multiple platforms and forums. Services claim to scan for your information across the dark web, but they typically alert you only when your data appears in newly indexed breaches-long after criminals may have already accessed it. A WIRED investigation found that vendors routinely overstate dark web monitoring capabilities, unable to monitor all sources continuously. The service you pay for watches for new exposures, not the existing ones that matter most.
Coverage Gaps Beyond Credit Reports
Services completely miss entire categories of identity theft that never touch credit reports. Unauthorized bank transfers, wire fraud, and account takeovers on payment platforms operate outside the credit monitoring net entirely. According to FTC data, financial fraud that bypasses credit reports represents a growing share of identity theft cases, yet most protection plans focus exclusively on credit-based threats. Your bank account can drain while your credit report remains untouched.
Hidden Limits in Insurance Coverage
The insurance component further reveals the gap between marketing and reality. Services advertise up to $1,000,000 in coverage, but sub-limits create the actual protection ceiling. Many plans exclude cryptocurrency entirely unless you pay for specialized add-ons, leaving digital asset losses unprotected. Criminal identity theft-where someone uses your name to commit crimes-falls outside coverage at most providers because it doesn’t generate financial losses to reimburse. Medical identity theft, another growing threat, often isn’t covered under standard plans. The WIRED analysis found that common exemptions include cyber extortion, cyberbullying, and title fraud, which can significantly narrow what’s actually protected.
Building Your Real Defense Strategy
You cannot rely on any single service to cover your entire risk profile. A service that appears comprehensive on paper may leave you exposed to the exact fraud scenario you face. This reality makes layered protection essential-combining what these services offer with strategies you control directly. The next section shows you which protections actually work and how to implement them without depending on any single vendor.
What Actually Works to Stop Identity Theft
Credit Freezes Block New-Account Fraud at Zero Cost
Credit freezes represent the single most effective tool you control, yet most people never use them. A credit freeze blocks access to your credit report entirely, preventing criminals from opening new accounts in your name because lenders cannot pull your file to approve applications. The FTC Consumer Sentinel Network data shows new-account fraud drives significant losses, and freezes eliminate this threat at zero cost. You contact Equifax, Experian, and TransUnion directly to freeze your credit in minutes through their websites. The process takes about 15 minutes total across all three bureaus. If you need to apply for legitimate credit, you temporarily unfreeze your report with a PIN code you receive during the initial freeze. This isn’t passive monitoring-it’s active prevention. The GAO evaluated identity theft services after major breaches and concluded that lower-cost alternatives like credit freezes often outperform expensive monitoring subscriptions at preventing new-account fraud. If you’re not actively applying for new credit, a freeze should be your baseline protection, not an afterthought.
Two-Factor Authentication Stops Account Takeovers
Two-factor authentication creates a barrier that monitoring services cannot replicate. When criminals access your email or bank login credentials through phishing or data breaches, two-factor authentication blocks them from entering your accounts even with the correct password. The FBI Internet Crime Report for 2024 identified phishing as a top fraud category, yet two-factor authentication defeats most phishing attacks because stolen credentials alone don’t grant access. Enable two-factor authentication on every financial account, email address, and platform storing sensitive data. Use authenticator apps like Google Authenticator or Authy rather than text message codes when possible-SIM swapping attacks can intercept text messages, but authenticator apps remain secure. This single step eliminates the most common account takeover vector that identity theft protection services cannot prevent. Many banks offer two-factor authentication as a standard feature you activate in account settings, costing nothing but requiring five minutes of setup per account.
Weekly Account Reviews Catch Fraud Before It Spreads
Monitoring services alert you to credit report changes, but they cannot see unauthorized transactions in real time. Log into your bank accounts and credit cards weekly, reviewing transactions line by line. This practice catches wire fraud, unauthorized purchases, and account transfers before criminals drain significant balances. The median identity theft loss recorded by the FTC Consumer Sentinel Network in 2024 was $497, but about 124,000 reports involved losses exceeding $10,000-most of those losses could have been stopped within days if discovered early.
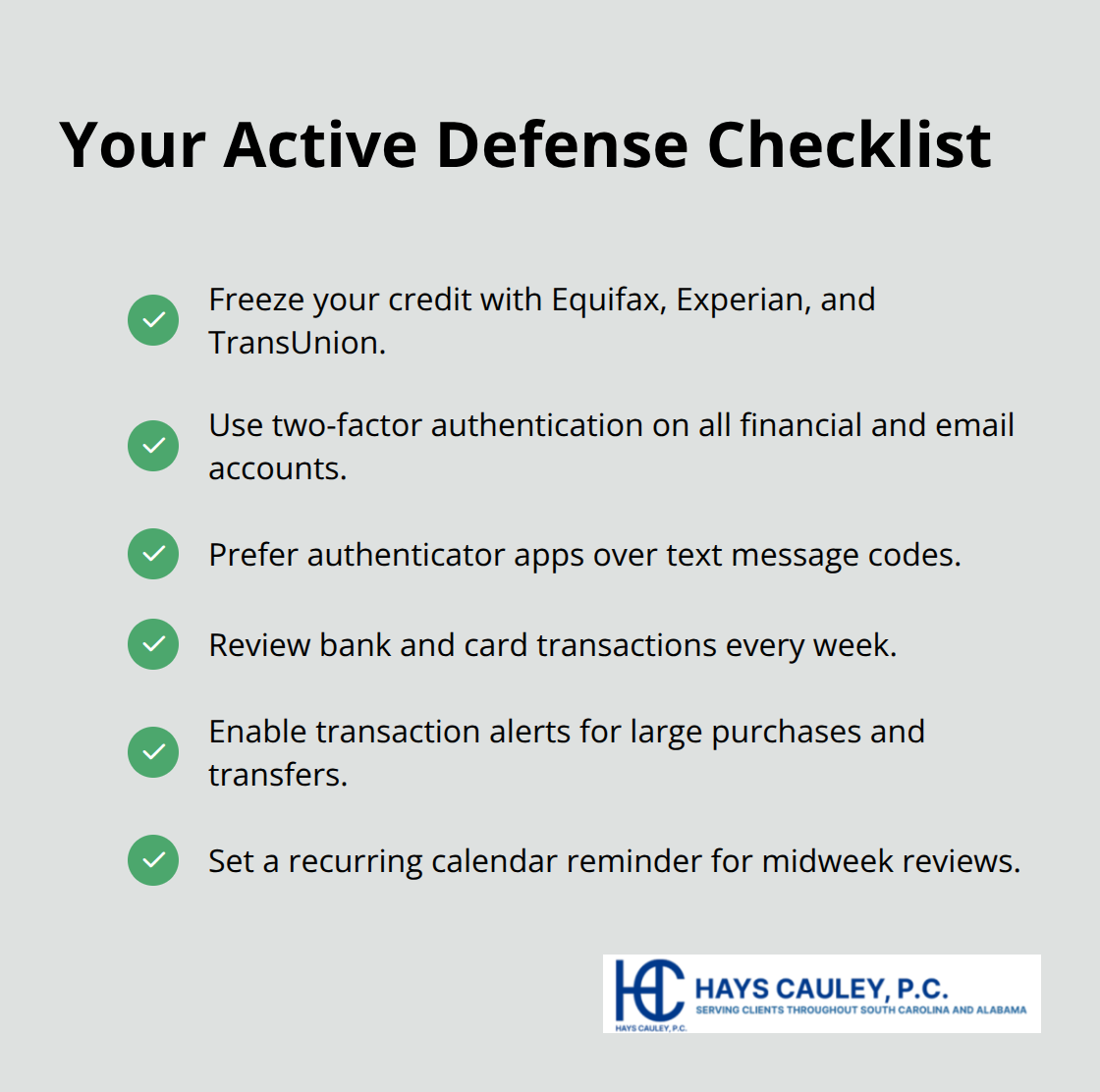
Set calendar reminders for Wednesday or Thursday each week to review accounts when you have time. Many banks offer transaction alerts you can customize to notify you immediately of purchases over a certain threshold or any transfers from your account. Configure these alerts and check them daily. This active approach works because you respond faster than any monitoring service’s alert system, and you see unauthorized activity before it accumulates into catastrophic losses.
Final Thoughts
Identity theft protection services monitor for fraud after criminals strike, but they cannot prevent identity theft from happening in the first place. The insurance they offer reimburses expenses rather than stolen funds, and the dark web scanning they advertise cannot track billions of already-exposed records. Coverage contains hidden limits that exclude cryptocurrency, criminal identity theft, and medical fraud, leaving significant gaps in what these services actually protect.
What stops identity theft is what you control directly through credit freezes, two-factor authentication, and weekly account reviews. Credit freezes block new-account fraud at zero cost by preventing lenders from accessing your credit file, while two-factor authentication defeats account takeovers even when criminals possess your passwords. Weekly reviews of your bank and credit card accounts catch unauthorized transactions before they accumulate into substantial losses, and transaction alerts notify you immediately of suspicious activity.
The strongest defense combines identity theft protection services with your own active protections rather than relying on any single solution. Freeze your credit when you’re not applying for new credit, enable two-factor authentication on every financial account and email address, and configure transaction alerts on your bank accounts. If you fall victim to identity theft despite these precautions, Hays Cauley, P.C. helps consumers recover from fraud and protect their financial future.


