Identity theft is growing faster in South Carolina than many residents realize. Criminals are targeting personal information through data breaches, phishing scams, and stolen documents at an alarming rate.
At Hays Cauley, P.C., we help South Carolina residents understand how identity theft monitoring can protect them from financial loss and fraud. This guide covers what you need to know to stay protected.
The Growing Identity Theft Crisis in South Carolina
South Carolina faces an identity theft epidemic that demands immediate attention. According to the South Carolina Department of Consumer Affairs, residents lost over 8 million dollars to scams and identity theft in 2025 alone. The state now ranks 11th nationally for identity theft cases, with 17,396 reports already logged in 2025-a number that has already surpassed the entire full-year total for 2024. This means approximately 64 South Carolina residents become identity theft victims every single day, or roughly one victim every 22.5 minutes. The acceleration is striking: 2025 year-to-date totals have already reached 115% of the previous year’s complete figures, signaling a sharp and troubling upward trend.
What Criminals Are Stealing From South Carolina Residents
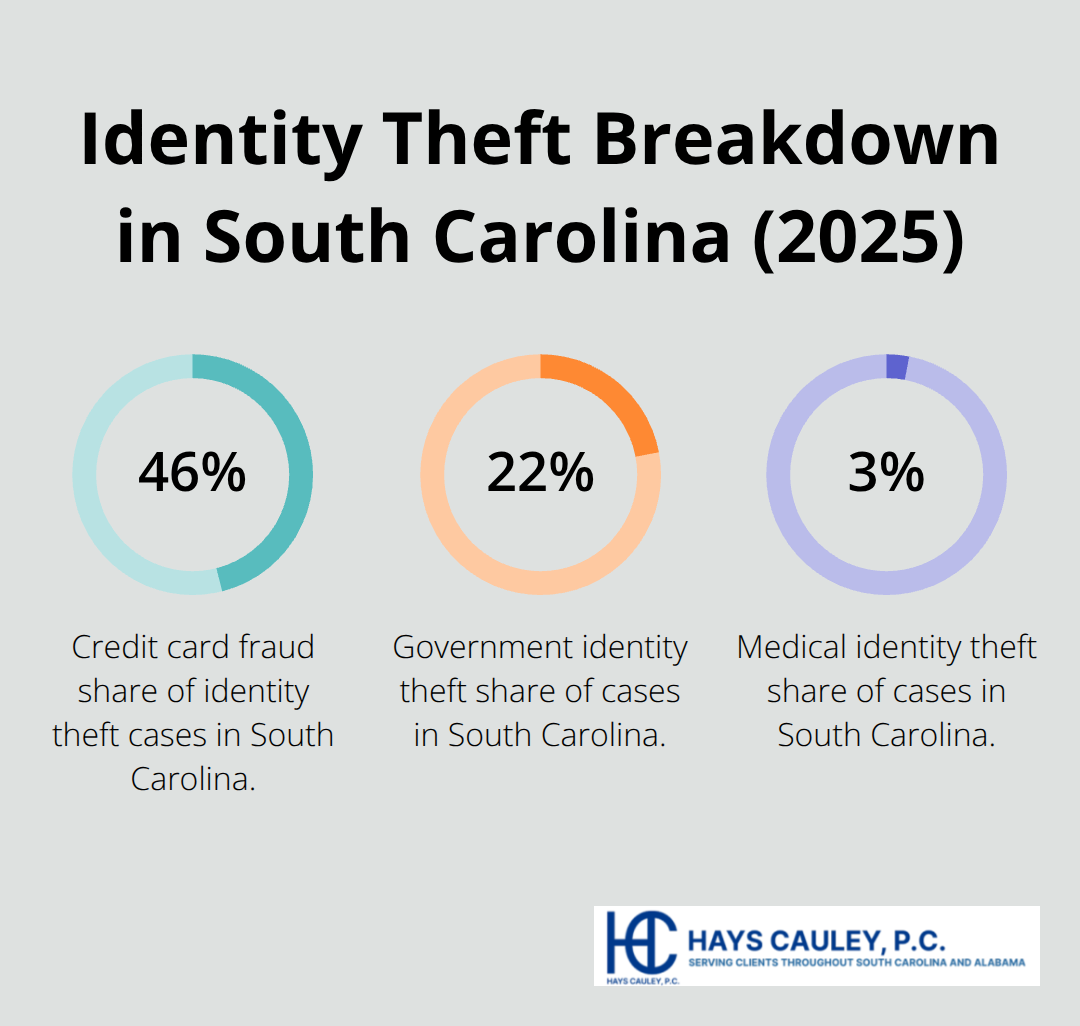
Credit card fraud dominates the landscape, accounting for 7,978 reports and 45.9% of all identity theft cases in the state. Other identity theft types follow closely behind with 5,541 reports, while loan or lease fraud rounds out the top three with 3,784 reports. Financial identity theft accounts for approximately 60% of all South Carolina cases, government identity theft represents 21.74%, and medical identity theft makes up 2.85% of cases.
Criminals use diverse and persistent methods: purchase scams, service and repair scams, and debt collection scams represent the most prevalent categories targeting residents. Approximately 60% of scam-reporting consumers were initially contacted by phone, making voice calls a primary attack vector that criminals exploit with alarming frequency.
The Real Cost of Becoming a Victim
The financial impact varies dramatically by age group, with the oldest residents bearing the heaviest burden. Residents aged 70 to 79 experience the highest total losses at approximately 15.6 million dollars combined, with a median individual loss of 800 dollars across 2,454 reports. Those aged 60 to 69 also face substantial risk, with 3,359 reports, a median loss of 526 dollars, and total losses reaching 14 million dollars. Victims typically discover the theft through credit reports, bank notices, and business notifications-often weeks or months after the crime occurs. The emotional toll compounds the financial damage: victims face stress from resolving fraudulent accounts, dealing with creditors, and managing the lengthy recovery process.
Why Monitoring Services Become Essential
The speed at which criminals act means that traditional detection methods fall short. Victims who wait for statements or credit reports to arrive already face weeks of unauthorized activity on their accounts. Real-time monitoring systems alert residents to suspicious activity the moment it occurs, allowing them to respond before criminals cause extensive damage. This rapid notification capability transforms how residents protect themselves from the escalating threat landscape in South Carolina.
What Features Actually Stop Identity Theft: Serving South Carolina, including Greenville, Columbia and Charleston
The Three Core Capabilities That Matter Most
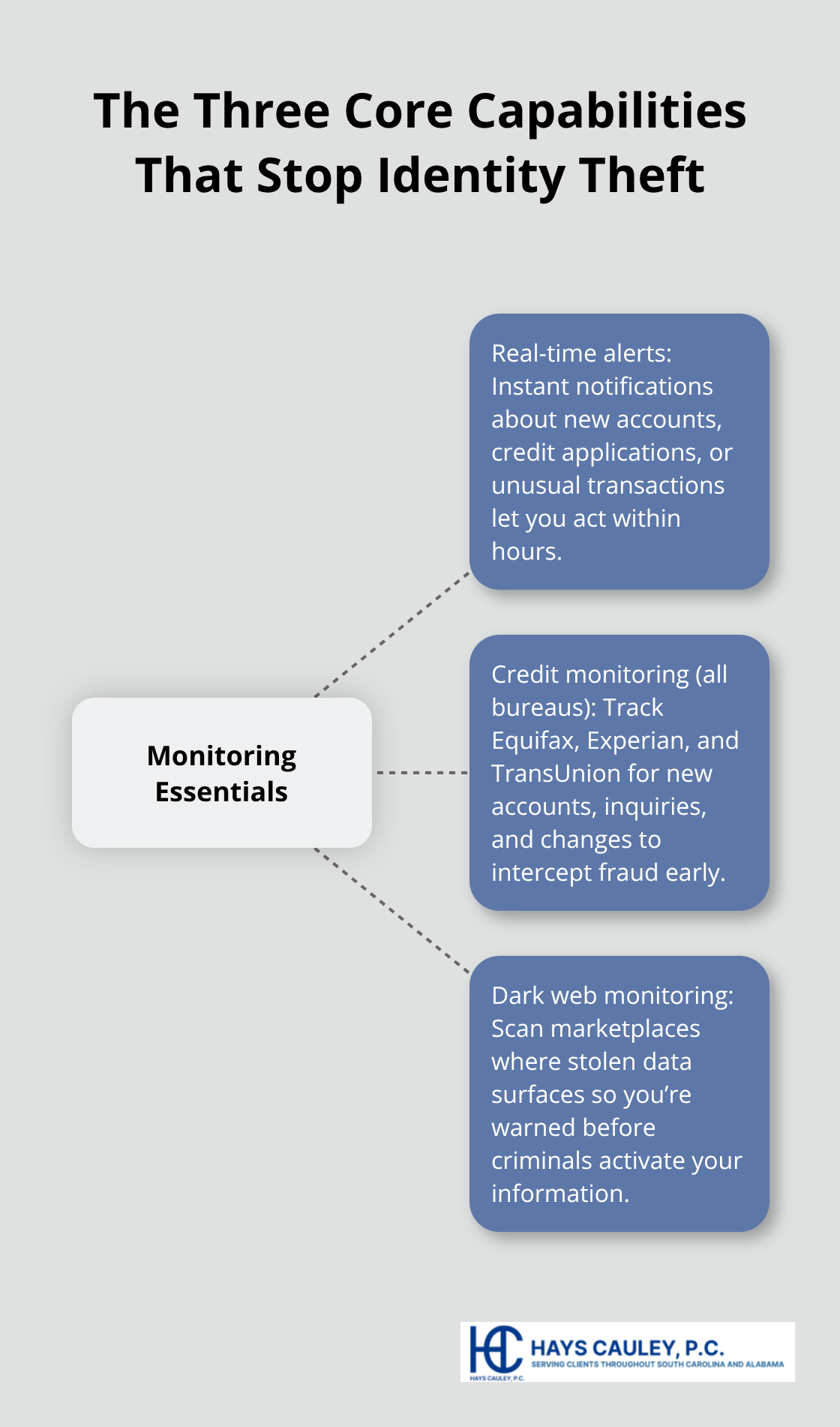
Monitoring services flood the market with promises, but most South Carolina residents don’t understand which features genuinely protect them and which ones merely sound impressive. The most effective services combine three core capabilities that work together: immediate alerts when suspicious activity occurs, continuous surveillance of your credit reports, and surveillance of the dark web where stolen data typically surfaces first. Real-time alerts matter because criminals move fast-they open fraudulent accounts within hours of stealing your information. When you receive an alert instantly rather than discovering fraud weeks later on a statement, you can contact creditors immediately and prevent thousands in unauthorized charges.
Real-Time Alerts Stop Criminals Before They Cause Damage
Services like Norton, Aura, and NordProtect all offer 24/7 real-time alerts tied to your credit files and financial accounts, though alert quality varies significantly between providers. These alerts notify you the moment someone attempts to open a new account, apply for credit, or make unusual purchases in your name. The speed of notification transforms your ability to respond-criminals who expect a 30-day delay before you notice fraud find themselves blocked within hours.
This rapid response capability represents the single most valuable feature any monitoring service provides, since it directly prevents financial loss rather than simply documenting it after the fact.
Credit Monitoring Catches Fraudulent Accounts Across All Three Bureaus
Credit monitoring watches all three major bureaus-Equifax, Experian, and TransUnion-for new accounts, inquiries, and changes that signal fraudulent activity. This matters because criminals in South Carolina often create new credit lines in victims’ names, and the monitoring catches these before they damage credit scores permanently. When you monitor all three bureaus simultaneously, you eliminate the gaps that criminals exploit. A fraudster might open an account at one bureau while you only watch another, but comprehensive monitoring prevents this strategy from succeeding.
Dark Web Monitoring Catches Fraud at Its Source
Dark web monitoring represents the feature that catches fraud earliest in the criminal pipeline. Stolen data sells on dark web marketplaces within days of a breach, and services that scan these locations alert you before criminals activate your information. OmniWatch Identity Theft Protection, for example, includes dark web surveillance alongside up to 2 million dollars in identity theft insurance and white-glove recovery assistance-critical given that 70 to 79-year-old South Carolina residents lose a median of 800 dollars per case according to the South Carolina Department of Consumer Affairs. However, insurance coverage typically reimburses administrative costs like legal fees rather than replacing stolen funds directly, so prevention through monitoring matters more than recovery through claims.
Combine Automated Monitoring With Your Own Quarterly Reviews
The strongest approach combines automated monitoring with your own quarterly credit report reviews, which you can obtain free from the three major bureaus. This combination catches both known breaches and undiscovered fraud simultaneously, giving you the speed and redundancy that criminals struggle to overcome. Your personal review adds a human perspective that automated systems sometimes miss-you recognize accounts you never opened or inquiries from companies you never contacted. When you pair this manual oversight with real-time alerts and dark web scanning, you create multiple defensive layers that force criminals to work much harder to succeed.
Defend Your Information Where Criminals Hunt First
Phone Calls Remain the Primary Attack Vector
Monitoring services catch fraud after it happens, but your real defense starts before criminals target you. South Carolina residents need to understand that the documents in your home, your email inbox, and your financial accounts represent the actual entry points criminals exploit. The South Carolina Department of Consumer Affairs reports that about 60% of scam victims in the state received initial contact by phone, meaning criminals often call to extract information directly rather than stealing it from a database. This reveals something critical: your own vigilance matters more than any automated system.
Criminals call pretending to be from banks, government agencies, or utility companies, and they excel at creating urgency that bypasses your skepticism. Never share personal information over the phone unless you initiated the call and verified the number through official channels, not through a number the caller provided. If someone calls claiming to be from your bank, hang up immediately and call the number on your bank statement or the back of your card. This single practice stops the majority of phone-based identity theft attempts before they start.
Quarterly Credit Report Reviews Catch Fraud Early
Your financial accounts require quarterly reviews that go far beyond glancing at statements. The South Carolina Department of Consumer Affairs found that victims commonly learn of identity theft through credit reports, bank notices, and business notifications, which means you’re already weeks behind when you discover fraud passively. Pull your free credit reports from all three bureaus every four months, rotating through Equifax, Experian, and TransUnion so you maintain continuous coverage throughout the year.
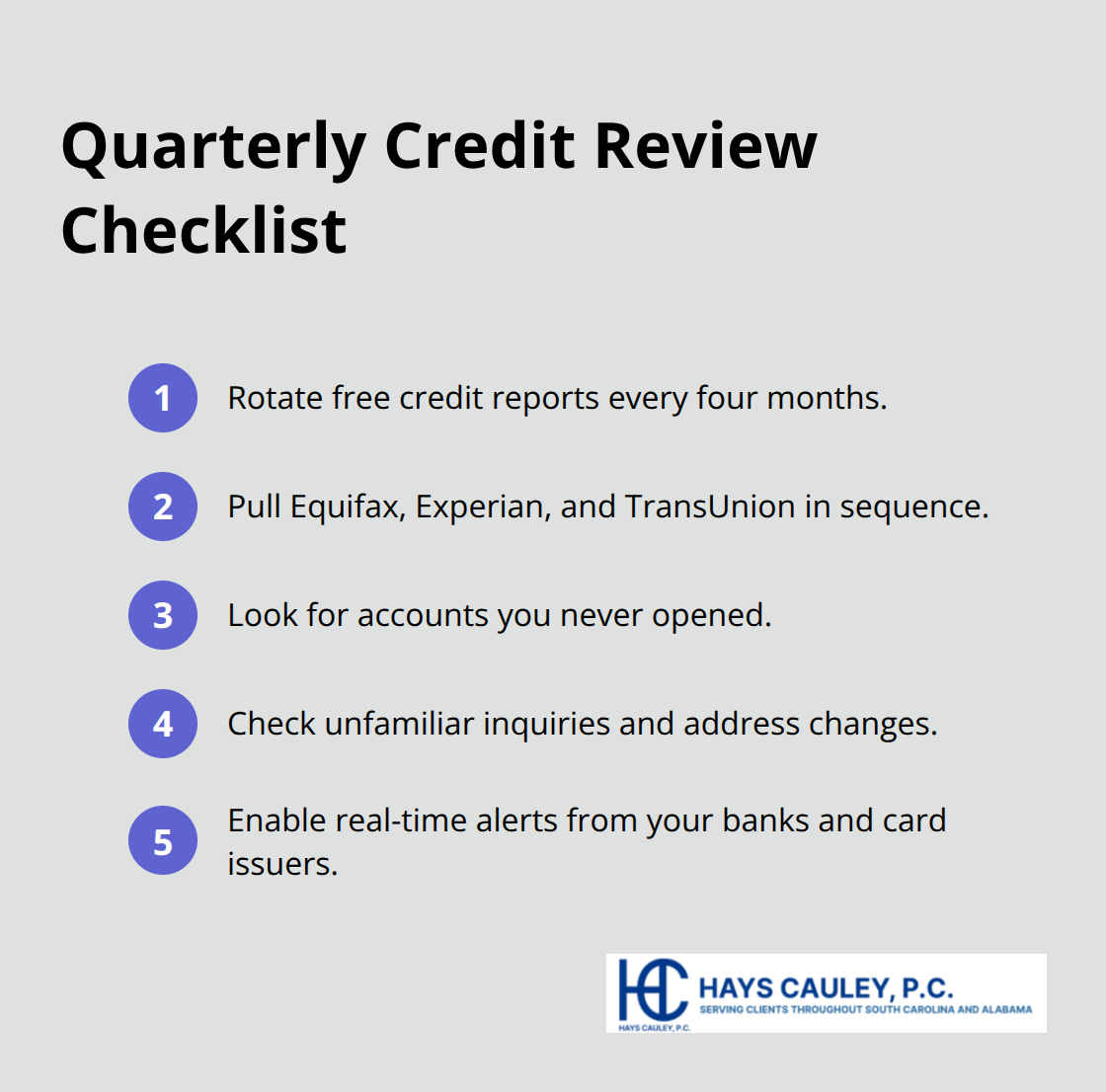
Look specifically for accounts you never opened, inquiries from companies you never contacted, and address changes you didn’t authorize.
When you review your bank and credit card statements within 24 hours of transactions, you catch fraudulent charges before they compound. Enable real-time alerts from your banks and credit issuers immediately, and set these alerts low enough to catch unusual activity. For credit cards used during travel or at high-volume merchants like gas stations where skimming occurs frequently, review charges within hours rather than days.
Strong Passwords and Two-Factor Authentication Create Layered Defense
Strong passwords represent your final practical defense layer, and this means passwords that use combinations of uppercase letters, numbers, and symbols with at least 16 characters. Password managers like Bitwarden or 1Password store these complex passwords securely so you never reuse weak ones across accounts. Two-factor authentication on financial accounts, email, and government portals adds a second security layer that makes account takeover substantially harder.
Use authenticator apps rather than text message codes when possible, since criminals in South Carolina have used SIM-swapping attacks to intercept text codes and gain access to accounts. These three practices-verifying callers independently, reviewing accounts quarterly, and securing access with strong passwords and two-factor authentication-create defenses that work whether or not you subscribe to a monitoring service.
Final Thoughts
South Carolina residents face an identity theft crisis that demands immediate action. With 64 victims every single day and losses exceeding 8 million dollars in 2025 alone, the threat is neither theoretical nor distant. Credit card fraud, loan schemes, and government identity theft target residents across every age group, though seniors aged 70 to 79 suffer the heaviest financial burden with median losses of 800 dollars per case.
Identity theft monitoring SC services provide genuine protection by catching fraud at three critical points: when criminals attempt to open accounts in your name, when stolen data surfaces on the dark web, and when unauthorized activity appears on your credit reports. Real-time alerts matter because they compress the window between theft and detection from weeks down to hours, allowing you to contact creditors and prevent thousands in unauthorized charges before criminals cause extensive damage. Your own quarterly credit reviews, phone call verification practices, and strong password management create defensive layers that work independently of any service.
The strongest protection combines automated monitoring with personal vigilance. Enable real-time alerts from your banks and credit issuers, pull your free credit reports every four months from all three bureaus, and never share personal information over the phone unless you initiated the call. If you discover you are a victim of identity theft, contact Hays Cauley, P.C. to discuss your situation and explore your options for recovery and protection moving forward.


