Identity theft costs Americans over $20 billion annually, and businesses face serious legal consequences for failing to prevent it. The Identity Theft Red Flags Regulation requires financial institutions and creditors to identify and respond to warning signs of fraud before accounts are compromised.
At Hays Cauley, P.C., we help South Carolina businesses, including those in Greenville, Columbia and Charleston, understand and implement these mandatory protections. This guide walks you through what the regulation demands, which red flags matter most, and how to build a compliance program that actually works.
What the Red Flags Rule Actually Demands
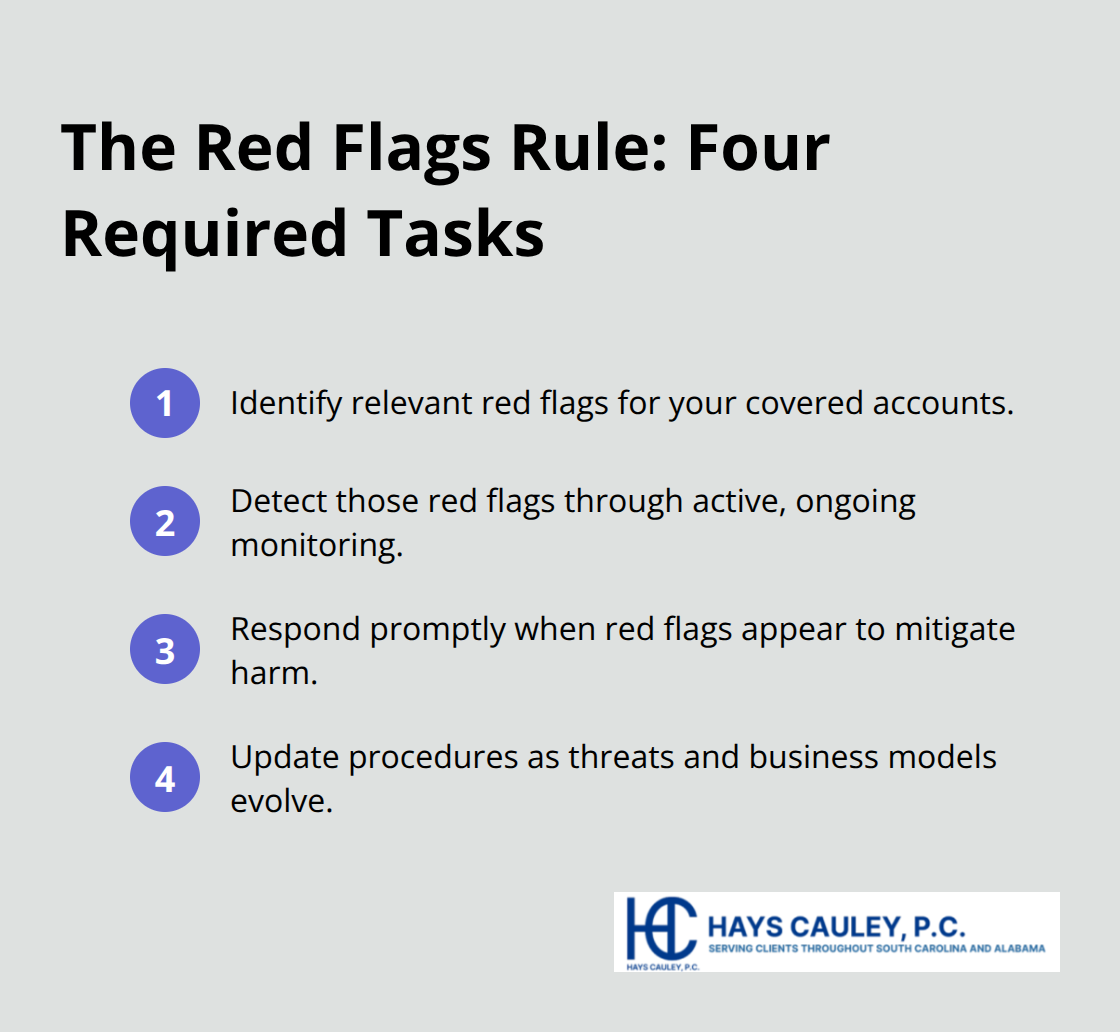
The Red Flags Rule, formally codified as 16 CFR Part 681, requires financial institutions and creditors to implement a written Identity Theft Prevention Program tailored to their size and operations. This isn’t a checkbox exercise-the FTC enforces violations with penalties up to $3,500 per violation, making compliance a genuine financial obligation. Your program must accomplish four specific tasks: identify red flags relevant to your accounts, detect those flags through active monitoring, respond when flags appear, and update procedures as threats evolve. The rule applies to any organization maintaining covered accounts, which includes credit cards, mortgages, auto loans, checking accounts, savings accounts, and any other accounts involving multiple payments or transactions.
If your business extends credit or uses consumer reports in credit decisions, you likely fall under this regulation. The FTC’s guidelines emphasize that compliance depends on the nature of your accounts, not your industry classification, meaning a retail business offering financing carries the same obligations as a traditional lender.
Who Needs an Identity Theft Prevention Program
Financial institutions like banks, credit unions, and savings associations automatically trigger the rule’s requirements. However, creditors face broader exposure-the FTC defines creditors as entities regularly extending credit or furnishing consumer reports for credit transactions, which includes payday lenders, auto title lenders, and even some retail operations with payment plans. State-chartered credit unions fall under FTC jurisdiction rather than federal banking regulators, but compliance standards remain consistent. The critical threshold is whether your organization maintains covered accounts. If you offer only cash transactions or accounts with minimal fraud risk, you may not need a formal program, though periodic risk assessment remains prudent as business models change. Service providers who handle account activities on your behalf must meet identical standards-your contracts with third parties should explicitly require them to detect red flags and report suspicious activity back to you. This responsibility cannot be outsourced away; your organization remains accountable for what service providers do.
Why This Rule Exists and What Changed
Congress enacted the Fair Credit Reporting Act’s identity theft provisions after recognizing that nine million Americans fall victim to identity theft annually, according to FTC data. The Red Flags Rule emerged as the enforcement mechanism, requiring organizations to shift from reactive fraud response to proactive detection. Before this regulation, many businesses discovered fraud only after customers reported unauthorized charges or accounts were severely compromised. The rule fundamentally shifted that dynamic by mandating that you identify warning signs before damage occurs. Suspicious documents, inconsistent personal information, unusual account activity, and address discrepancies now require documented responses rather than informal handling. This proactive approach reduces both customer harm and your organization’s exposure to liability and operational costs from compromised accounts.
Understanding these foundational requirements sets the stage for recognizing which specific red flags demand your immediate attention in daily operations.
Red Flags That Signal Identity Theft in Your Business
Five Core Categories of Suspicious Activity
Detecting identity theft before it damages accounts requires understanding the specific warning signs that appear in your daily operations. The FTC’s Red Flags Rule identifies five core categories of suspicious activity, and each demands a documented response from your organization. Address discrepancies represent one of the most actionable red flags-when a customer’s mailing address changes and a new card request arrives within 30 days, card issuers must validate that address change before issuing the card.
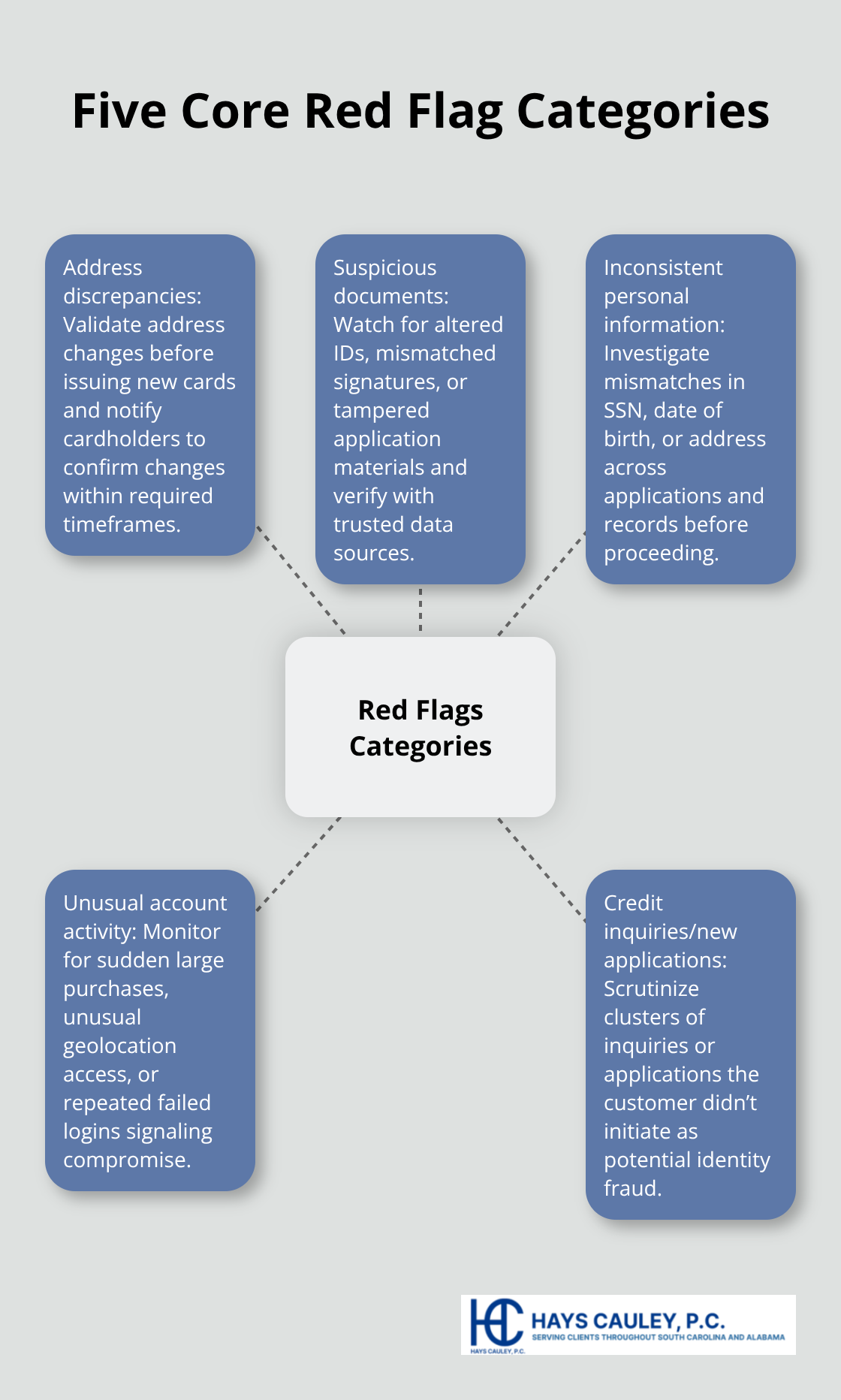
This simple procedure stops fraudsters who intercept new cards sent to altered addresses. Suspicious documents present another clear warning sign: altered or forged identification, mismatched signatures, or documents that appear tampered with during account opening. When staff encounters these documents, immediate verification through government-issued ID and cross-checks with third-party data sources like credit reports becomes mandatory.
Inconsistent Information and Weak Authentication
Inconsistent personal information creates a third category-when a customer’s Social Security number, date of birth, or address conflicts across applications or existing records, that mismatch warrants investigation rather than acceptance. The FTC emphasizes that relying solely on common identifiers like SSN or mother’s maiden name as authenticators leaves accounts vulnerable; layered verification using multiple independent sources provides stronger protection. Your staff should never process applications with mismatched information without additional verification. Multi-factor authentication and other strong authentication methods deter identity theft in high-risk online environments, particularly when customers access accounts remotely or request sensitive changes.
Transaction Monitoring and Account Activity Patterns
Unusual account activity and unauthorized transactions form critical red flags requiring active monitoring. Transaction patterns that deviate sharply from normal behavior-sudden large purchases, rapid account access from unusual geographic locations, or multiple failed login attempts-signal potential compromise. For existing accounts, continuous monitoring catches these patterns before customers discover fraud themselves. Credit inquiries and new account applications present distinct risks: multiple credit inquiries within a short timeframe, especially when the customer didn’t initiate them, indicate someone may be opening accounts fraudulently in your customer’s name.
Identity Verification During Account Opening
When opening new accounts, verification procedures must confirm the applicant’s identity matches submitted documents and cross-reference information against credit reports and the Social Security Administration’s Death Master File where applicable. The FTC reports that nine million Americans experience identity theft annually, yet many cases involve accounts opened fraudulently months before the legitimate account holder discovers the problem. Implementing detection procedures that catch these red flags during account opening, rather than waiting for customer complaints, dramatically reduces both fraud losses and regulatory exposure. If a company denies your dispute or refuses to acknowledge the fraud, your organization may face legal consequences, making proactive prevention essential to your compliance strategy.
Building a Compliance Program That Actually Protects Your Business
Your Identity Theft Prevention Program must move beyond documentation into operational reality. The FTC’s enforcement data shows that organizations with written programs but weak implementation face the same penalties as those with no program at all, so your strategy should focus on creating systems your staff actually uses daily. Start with a formal risk assessment to identify which accounts your organization maintains and which red flags pose genuine threats to those accounts. This assessment becomes your foundation-it determines whether you need a comprehensive program or a scaled approach for lower-risk operations. Document this assessment in writing and update it annually or whenever your business model changes, such as adding new account types or integrating service providers. The FTC emphasizes that your program must be tailored to your organization’s specific size and complexity rather than adopting generic templates that ignore your actual operations.
Assign Leadership and Establish Clear Accountability
Assign one staff member as your program officer responsible for overseeing implementation, reporting to senior management, and coordinating updates. This person should not be the only individual aware of the program’s requirements; dispersing knowledge prevents compliance gaps when staff members leave or take leave. Board or senior management must approve the initial program and receive periodic updates on effectiveness, incidents detected, and any regulatory changes affecting your obligations.
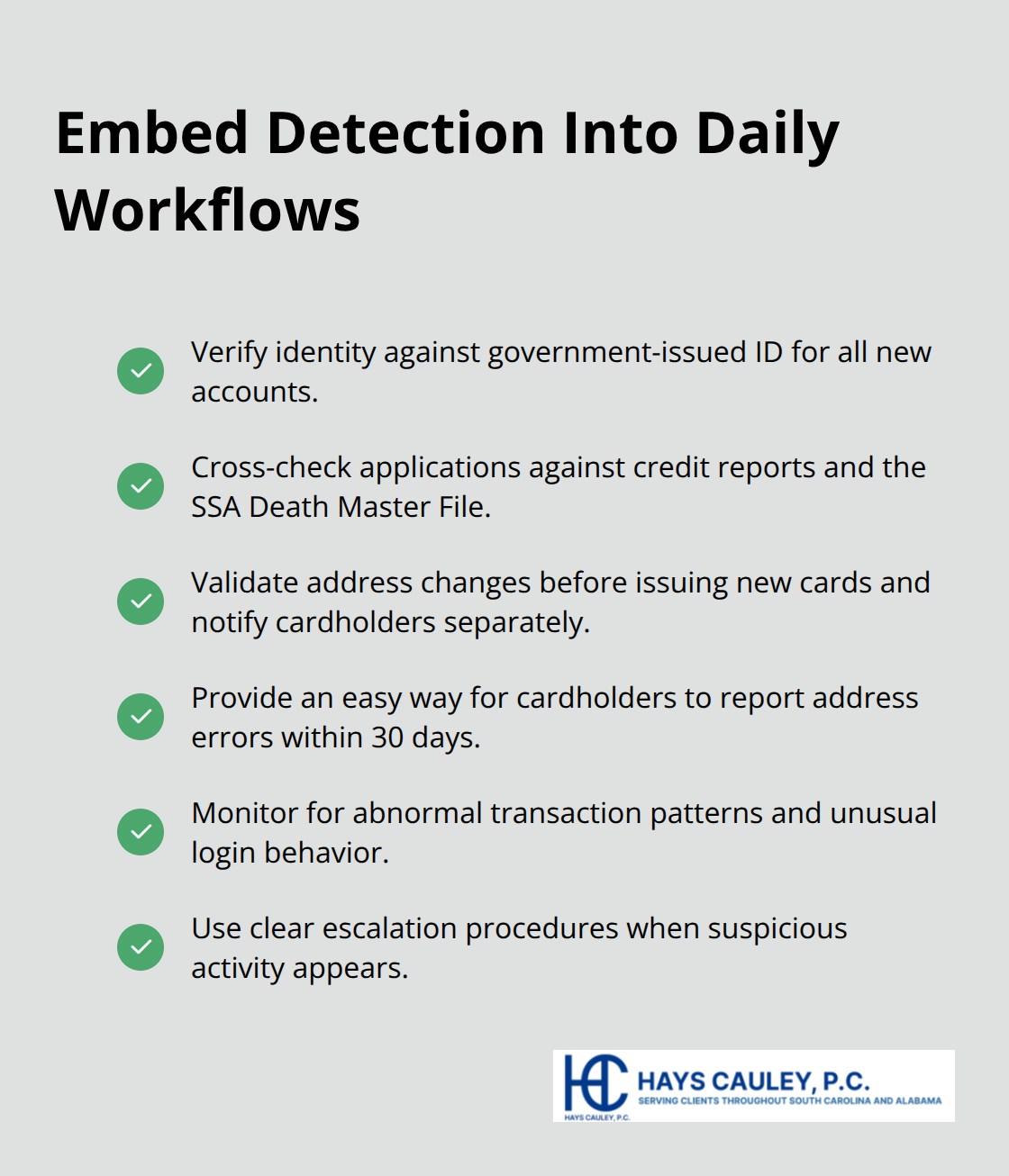
Embed Red Flag Detection Into Daily Workflows
Your detection procedures must integrate red flag identification into existing workflows rather than creating separate processes. When staff open accounts, they verify identity against government-issued identification and cross-reference information against credit reports and the Social Security Administration’s Death Master File. For address changes on existing accounts, implement mandatory validation procedures before issuing new cards-the FTC requires card issuers to notify cardholders separately about address changes and provide a means to report errors within 30 days. Train staff to recognize transaction patterns that deviate from normal customer behavior and establish clear escalation procedures when suspicious activity appears.
Strengthen Authentication and Response Procedures
Implement multi-factor authentication for high-risk online account access, particularly for password resets or sensitive account modifications. Your response procedures should specify exactly what happens when red flags appear-some situations warrant immediate account closure and law enforcement notification, while others require customer contact and monitoring. Document every response and maintain records for FTC review. Update your program at least annually to reflect emerging fraud methods, changes in your account offerings, and lessons learned from incidents.
Oversee Service Provider Compliance
Service provider contracts must explicitly require those vendors to implement identical red flag procedures and report suspicious activity to you, not just handle it independently. Your organization remains accountable for what service providers do, so monitor their compliance with the same rigor you apply to internal staff. Verify that contracts include specific language about red flag detection, response protocols, and regular reporting requirements back to your organization.
Final Thoughts
The Identity Theft Red Flags Regulation demands that your organization shift from reactive fraud response to proactive detection embedded in daily operations. When staff verify identity during account opening, monitor transaction patterns for existing accounts, and validate address changes before issuing new cards, you catch fraud before customers suffer damage. This approach protects your customers while simultaneously shielding your organization from the financial and reputational consequences of compromised accounts, with penalties reaching $3,500 per violation.
Start with a formal risk assessment to identify which accounts your organization maintains and which red flags pose genuine threats. Assign clear accountability through a designated program officer and ensure board-level oversight of implementation and updates. Document your procedures, train staff thoroughly, and monitor service providers with the same rigor you apply internally, updating your program annually to reflect emerging fraud methods and changes in your business operations.
We at Hays Cauley, P.C. help South Carolina businesses, including those in Greenville, Columbia and Charleston, navigate identity theft issues and consumer protection compliance. If you need guidance implementing your Identity Theft Prevention Program or addressing fraud incidents, contact us for assistance.


