Identity theft costs U.S. businesses over $15 billion annually, according to the FBI. Your company’s financial data, customer information, and reputation are all at risk.
We at Hays Cauley, P.C. understand that business identity theft protection requires immediate action and ongoing vigilance. This guide walks you through prevention strategies, warning signs, and recovery steps to safeguard your operations.
How Identity Theft Impacts Your Business: Serving South Carolina, including Greenville, Columbia and Charleston
Business identity theft creates three distinct layers of damage that most companies underestimate until they experience it. The immediate financial hit is severe-fraudsters open accounts in your company’s name, take out loans against your EIN, or file false tax returns. The IRS reports that inability to e-file because a return was already filed with your EIN is a primary red flag of business identity theft. Recovery costs mount quickly: investigating the fraud, correcting credit reports, legal fees, and restoring systems drain resources fast.
Financial Losses Hit Hard and Persist
When fraudsters use your business identity, they don’t just steal money once. They establish ongoing access to credit in your name, creating liabilities that compound over time. A fraudulent loan taken in your company’s name appears on your business credit report, affecting your ability to secure legitimate financing. This credit damage can persist for years, making it harder to refinance existing debt or access capital for growth.
The costs of investigation and remediation are substantial. You’ll need forensic analysis to understand how the breach occurred, legal counsel to navigate the regulatory landscape, and IT resources to close vulnerabilities. These professional services easily run into tens of thousands of dollars for a significant breach. Beyond the direct costs, your reputation suffers significant harm.
Reputation and Customer Trust Decline Rapidly
Customers lose confidence when they learn their data was compromised, and that trust erosion translates directly to lost revenue. A data breach involving customer information creates lasting damage-people remember which companies failed to protect them. Your employees become concerned about working for a company with weak security, making recruitment harder. Partners and vendors reassess their relationship with you.
Media coverage amplifies the problem, and negative information spreads faster than corrections. Rebuilding trust requires years of consistent security improvements and transparent communication-far longer than it takes to lose it in the first place.
Legal and Regulatory Consequences Add Serious Liability
The third layer involves legal and regulatory consequences. Depending on your industry and the data involved, you may face fines for failing to notify affected customers, breach notification law violations, or compliance failures. If health data was compromised, HIPAA regulations trigger additional penalties. Your business also becomes liable for damages customers suffer from the identity theft-fraudulent charges on their accounts, damaged credit, or identity recovery costs they incur.
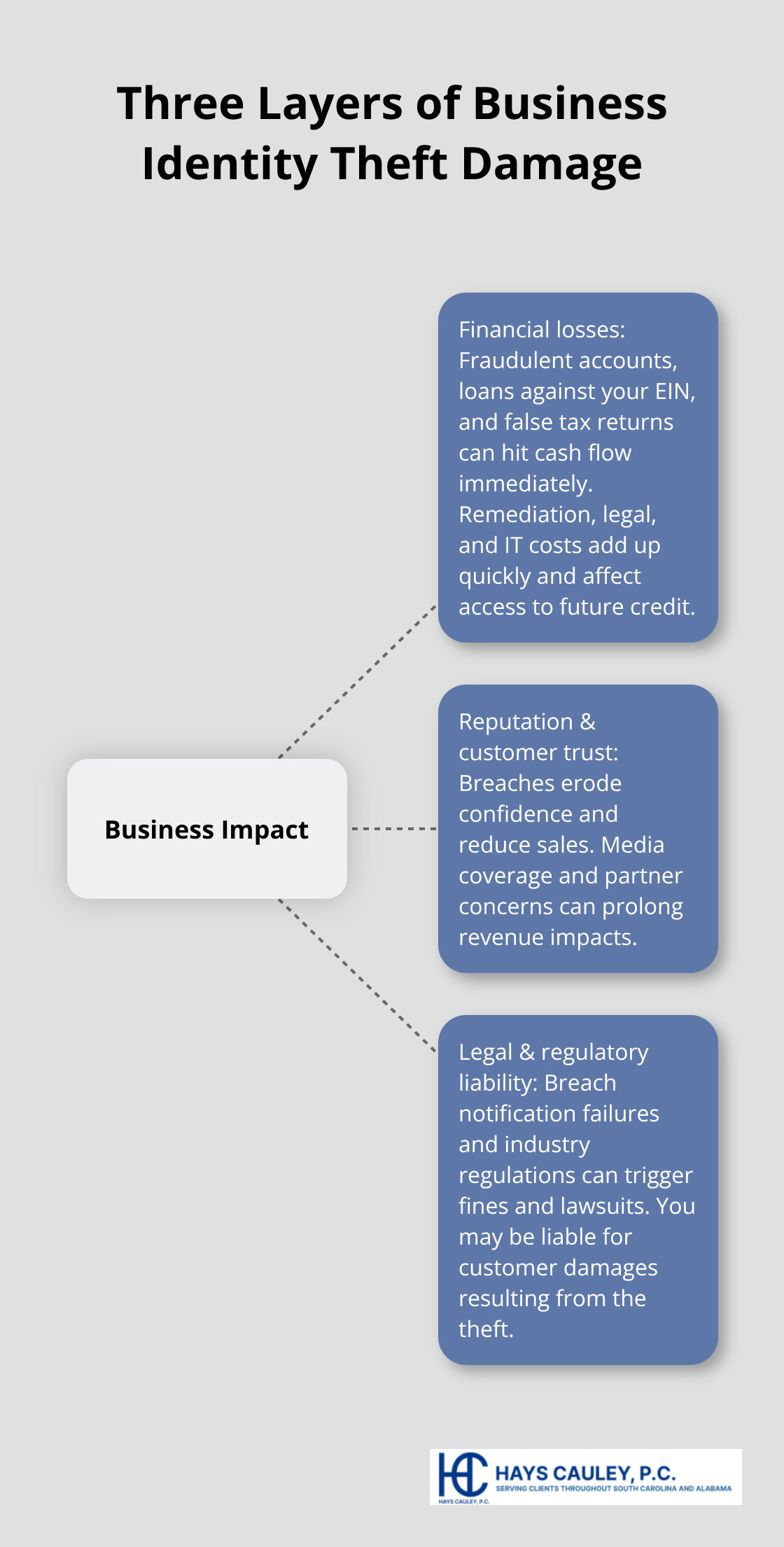
These three layers of damage compound each other. Financial losses reduce your ability to invest in security improvements. Reputation damage makes customers hesitant to do business with you. Legal liability creates ongoing financial and operational burdens. Understanding these consequences makes the case for prevention clear-the cost of prevention is far lower than the cost of recovery.
Build Your First Line of Defense Against Identity Theft: Serving South Carolina, including Greenville, Columbia and Charleston
Prevention stops identity theft before it drains your resources and damages your reputation. The foundation rests on three practical actions that directly reduce your vulnerability: controlling access to sensitive data, authenticating users properly, and monitoring for suspicious activity. Start by inventorying all personal information your business holds-customer data, employee records, financial information, tax documents, and anything stored across computers, cloud services, and paper files. This inventory reveals where your risk actually lives. Once you know what you have, apply the principle of least privilege: keep only what you genuinely need for operations and delete the rest. The FTC and NIST both recommend this approach because data you don’t hold cannot be stolen.
Lock Down Access Through Strong Authentication
Access control prevents fraudsters from using stolen credentials to open accounts or manipulate records in your name. Weak passwords are the entry point for most breaches-attackers use automated tools to crack simple passwords in minutes. NIST guidance recommends passwords with at least eight characters that include special characters and alphanumeric combinations, but passphrases work even better because they’re longer and easier to remember. Use a unique password for each account rather than recycling the same one across multiple services. A password manager solves the burden of remembering dozens of unique credentials while generating strong ones automatically.
Multi-factor authentication adds a second verification step that stops attackers even if they have your password. Enable MFA wherever available-email accounts, banking portals, cloud storage, accounting software. The extra 10 seconds to approve a login on your phone prevents unauthorized access far more effectively than any other single measure. Require employees to change passwords periodically and prohibit sharing credentials between staff members, even for convenience.

One shared admin account means you cannot track who made changes or detect when someone’s account is compromised.
Monitor Accounts and Credit for Red Flags
Catching identity theft early limits damage dramatically. Check your business credit report at least quarterly for accounts you did not open, inquiries from lenders you did not contact, or changes to your business address. The IRS identifies inability to e-file because a return was already filed with your EIN as a primary warning sign of business identity theft. Watch for unexpected tax transcripts or IRS notices that don’t match what you submitted. If the IRS sends letters 6042C or 5263C requesting information to validate your return or entity, respond immediately-these letters indicate the IRS detected suspicious activity on your account.
Sign up for electronic notifications from your bank, creditors, and service providers so you receive alerts about account changes in real time rather than discovering fraud weeks later. Unexpected credit inquiries, new accounts, or address changes trigger immediate investigation. This monitoring approach catches fraud within days rather than months, when recovery becomes exponentially harder and more expensive.
Secure Employee Data and Restrict Access
Your employees handle sensitive information daily, making them both your strongest asset and your greatest vulnerability. Limit access to personal data to only those individuals who need it for their specific job responsibilities. A customer service representative doesn’t need access to payroll records, and an accountant doesn’t need employee home addresses. Encrypt sensitive files and emails with strong password protection so that data remains unreadable if a breach occurs. When employees leave your company, immediately revoke their access to all systems and retrieve company devices. Forgotten access credentials create open doors for former staff or anyone who gains control of their old accounts.
Train your team on phishing awareness and safe handling of email attachments, since employees often represent the weakest link in your security chain. Spear phishing targets specific employees with convincing messages designed to steal credentials or install malware. Phone phishing uses social engineering to trick staff into revealing information or transferring funds. Regular training (even brief annual sessions) significantly reduces the likelihood that an employee will fall for these tactics and compromise your entire network.
The next section addresses what happens when prevention fails-the immediate steps you must take to contain damage and begin recovery.
What to Do When Your Business Falls Victim to Identity Theft: Serving South Carolina, including Greenville, Columbia and Charleston
The moment you discover identity theft, your response determines whether damage spreads or gets contained. Speed matters more than perfection. Assemble a breach response team immediately across forensics, legal, IT, operations, communications, HR, and management to prevent further data loss, according to FTC Data Breach Guidance. Start by taking affected equipment offline and stopping additional unauthorized access. Do not power down machines until your forensics team arrives-they need to capture forensic images and collect evidence while data remains intact. Monitor entry and exit points to your network, update all credentials, and replace compromised systems with clean machines if possible. Document everything you do during this response phase because you’ll need this evidence later for regulatory compliance and potential legal proceedings.
Contain the Breach Immediately
Contact your IT provider or a qualified cybersecurity firm immediately if you lack internal forensic capabilities. The goal during these first hours is containment: prevent the attacker from accessing more data or covering their tracks. Your forensics team identifies how the breach occurred, determines its scope, and outlines remediation steps. They also preserve evidence that law enforcement and regulators will need. Remove improperly posted information from the web and contact search engines to remove cached data. Scan for other copies of your data across the internet and remove them. This technical response happens in parallel with your legal and communications strategy.
Notify Law Enforcement and Legal Authorities
Consult legal counsel on federal and state privacy laws your breach implicates. Different industries face different requirements-health data triggers HIPAA regulations and the Health Breach Notification Rule, while financial data falls under different statutes. Your attorney helps determine which customers you must notify, what timeline applies, and what language your notification must contain.

Notify law enforcement promptly; if local police lack experience with information compromises, contact the FBI or U.S. Secret Service. For mail theft, contact USPS. State breach notification laws require you to notify affected individuals without unreasonable delay, though definitions vary by state.
Communicate Clearly With Affected Individuals
The FTC’s model letters for SSN breaches provide guidance on clear language describing what happened, what information was involved, actions you took, steps victims can take, and how to contact you. Provide a single point of contact, multiple notification channels, and ongoing updates on your website. Direct affected individuals to IdentityTheft.gov to report identity theft and receive an individualized recovery plan. Offer free credit monitoring or identity protection services and provide free credit reports from annualcreditreport.com with guidance on fraud alerts or credit freezes. If Social Security numbers were stolen, contact the major credit bureaus immediately to alert them about the breach.
Final Thoughts
Business identity theft protection requires consistent action, not one-time fixes. The strategies outlined in this guide-strong passwords, multi-factor authentication, regular monitoring, employee training, and rapid response protocols-form your defense against fraud. No single measure stops all threats, but layering these protections makes your business a harder target than competitors who neglect security.
Ongoing vigilance matters more than initial setup, since your threat landscape changes constantly as attackers develop new tactics and regulations evolve. Review your security practices quarterly, update software and systems promptly, and refresh employee training annually. Monitor your business credit report regularly for suspicious activity and stay informed about the latest identity theft threats affecting your industry.
When you face identity theft despite your prevention efforts, the response steps you take in the first hours determine your recovery timeline and total costs. We at Hays Cauley, P.C. help businesses navigate identity theft and credit reporting issues when they arise, and we understand the legal obligations you face after a breach and the steps required to protect your business and customers. Contact Hays Cauley, P.C. for support tailored to your situation.


