Your Social Security number is one of the most valuable pieces of personal information a criminal can steal. Understanding how does social security identity theft occur is the first step toward protecting yourself.
At Hays Cauley, P.C., we’ve seen firsthand how quickly identity theft can spiral into serious financial and legal problems for South Carolina residents. This guide walks you through the tactics criminals use, the warning signs to watch for, and the concrete steps you can take right now.
Where Criminals Get Your Social Security Number
Criminals obtain Social Security numbers through three primary pathways, and understanding each one helps you recognize your vulnerability. Data breaches remain the most common source-when hackers infiltrate company databases, they access millions of SSNs at once. The Federal Trade Commission reported 441,882 identity theft complaints in 2022 alone, with many traced back to compromised databases. Major breaches expose SSNs stored by retailers, healthcare providers, financial institutions, and government agencies. One notable incident involved 26.5 million veterans’ records stolen from an unencrypted laptop, which prompted federal agencies to require encryption of sensitive data on devices since 2006. The problem persists because many organizations still store SSNs without adequate protection or continue using SSNs as primary identifiers when they could switch to alternate identifiers that pose far less risk.
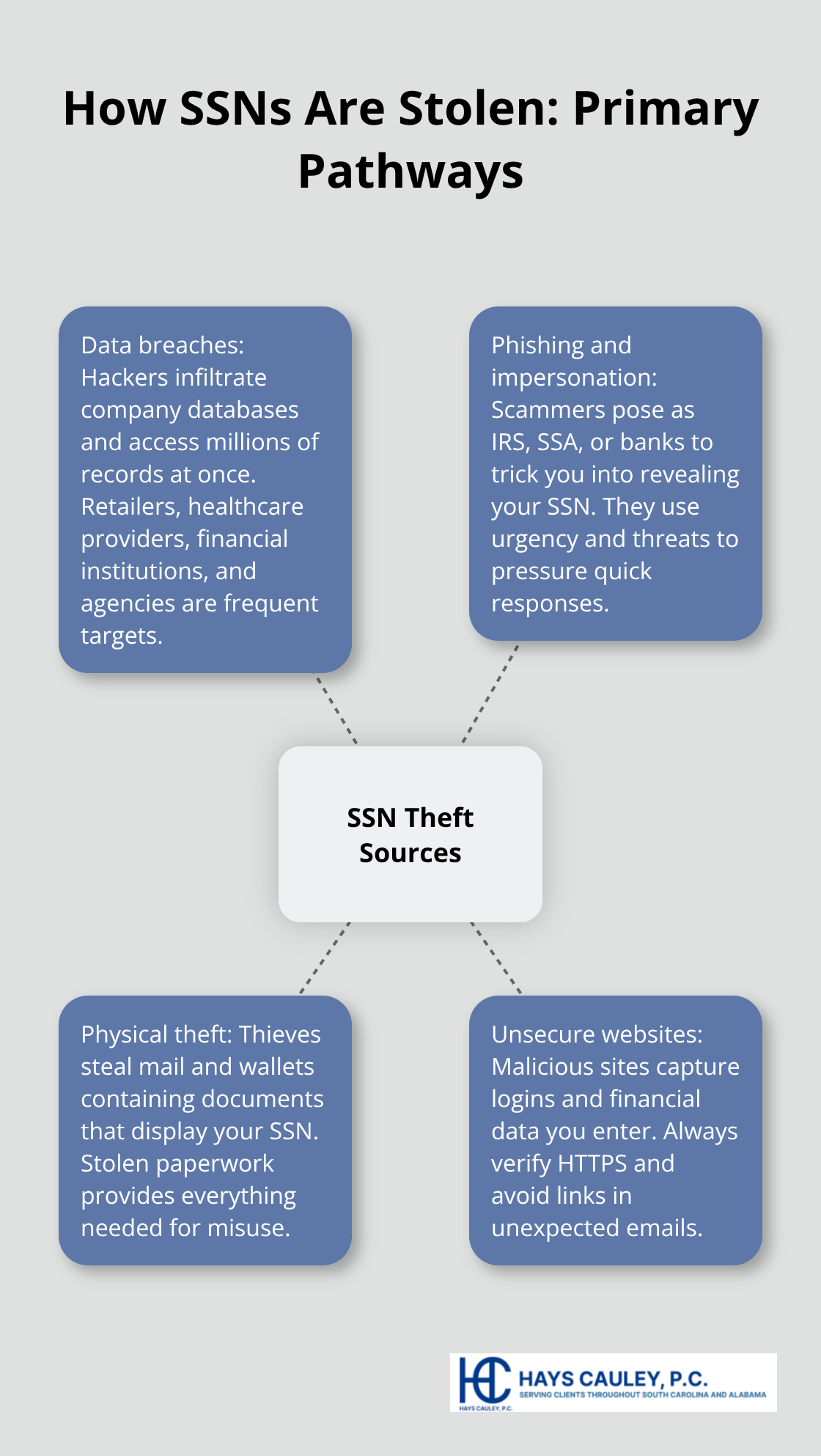
Data Breaches and Unprotected Systems
Hackers target companies that fail to encrypt sensitive information or maintain weak security protocols. When a breach occurs, criminals gain access to thousands or millions of SSNs simultaneously, creating a massive pool of potential victims. Organizations in healthcare, finance, and retail sectors face particular risk because they maintain extensive databases of customer SSNs. The 2006 federal encryption requirement emerged after the veterans’ records theft, yet many institutions still fail to comply fully. You cannot control whether a company protects your SSN, but you can monitor your credit reports and my Social Security account for suspicious activity that indicates your number has been compromised.
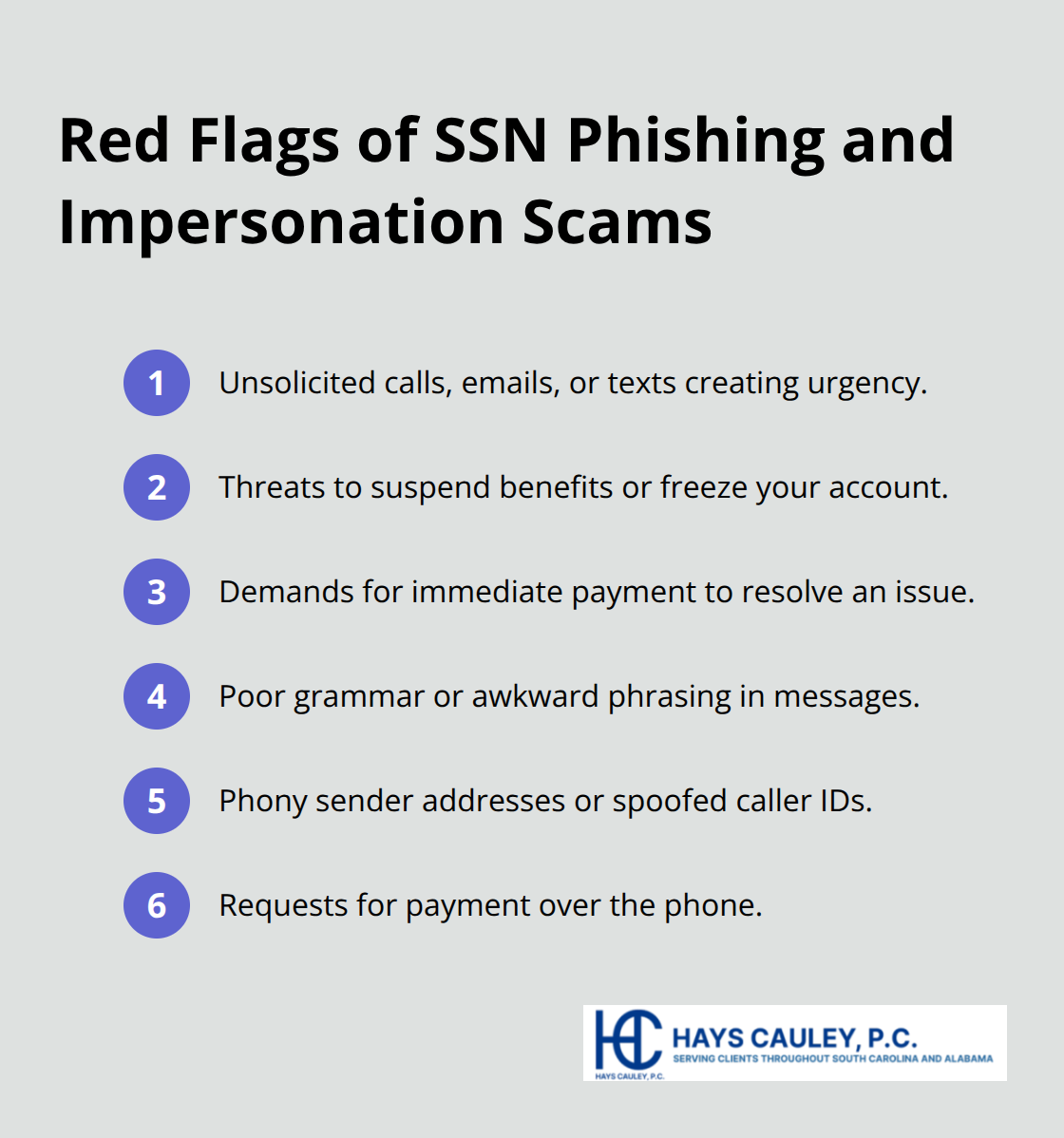
Phishing, Impersonation, and Scam Tactics
Scammers impersonate government agencies, banks, and legitimate companies to trick you into revealing your SSN directly. The Federal Trade Commission identifies government impersonation scams as particularly common, with criminals posing as IRS, Social Security Administration, or Medicare representatives. These scams typically involve unsolicited phone calls, emails, or text messages that create urgency-threatening to suspend your benefits, freeze your account, or demand immediate payment. Red flags include threats, poor grammar in emails, phony sender addresses, and requests for payment over the phone.
Physical Theft and Unsecure Websites
Physical mail theft and wallet theft remain effective methods for criminals to obtain your SSN. Thieves intercept documents containing your number or steal wallets containing identification cards that display it. Unsecure websites represent another vector-some sites host malicious code that captures login credentials and financial information when you enter them. Always verify that websites display HTTPS:// before entering personal details, and never click links in unexpected emails asking for financial information. These multiple attack vectors mean criminals have numerous opportunities to obtain your SSN, making detection of fraudulent activity the next critical step in protecting yourself.
What Criminals Do With Your Stolen Social Security Number
Once criminals have your SSN, they act fast to exploit it for maximum financial gain. The tactics they use fall into three main categories, each causing distinct damage to your finances and identity.
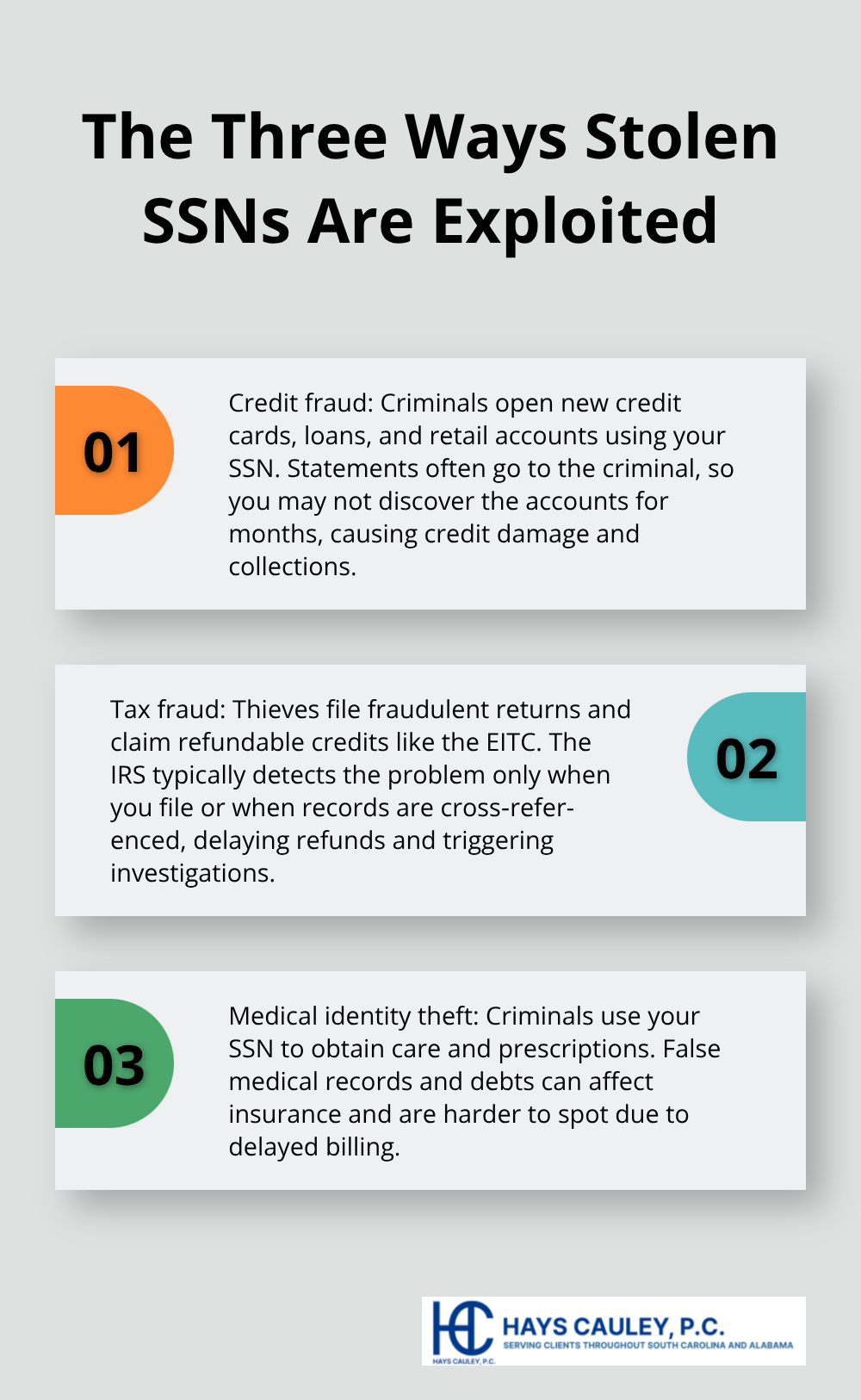
Opening Credit Accounts in Your Name
Criminals use your SSN to open new credit accounts, personal loans, auto loans, and retail accounts without your knowledge. Banks and lenders typically verify identity using your SSN and basic personal information, which criminals piece together from data breaches or public records. The Federal Trade Commission reported that in 2022, 441,882 identity theft complaints involved misuse of existing credit or fraudulent credit applications. You might not discover these accounts for months because statements go to the criminal’s address or email. The damage compounds quickly: fraudulent accounts tank your credit score, lenders deny your legitimate applications, and collection agencies pursue you for debts you never incurred.
Monitor your credit reports monthly through all three bureaus (Equifax, Experian, and TransUnion). Pull your free annual report at AnnualCreditReport.com and look for accounts you did not open, inquiries you did not authorize, and payment defaults on accounts you recognize. This monthly review catches fraudulent activity before it spirals into larger financial problems.
Filing Fraudulent Tax Returns Using Your SSN
Criminals file fraudulent tax returns using your SSN to claim refunds and redirect money to accounts under their control. The Social Security Administration Office of Inspector General documented cases where identity thieves filed returns claiming the Earned Income Tax Credit and other refundable credits. In one notable audit, SSA OIG found that about $742 million in self-employment earnings were removed from tax records due to identity theft, with many cases connected to misused SSNs and fraudulent EITC claims. These schemes are particularly dangerous because the IRS discovers the fraud only when you file your legitimate return or when the agency cross-references wage records.
Contact the IRS at 1-800-908-4490 if you suspect fraudulent tax filings. File an Identity Theft Report with the Federal Trade Commission at IdentityTheft.gov immediately to create an official record of the theft.
Obtaining Medical Services and Prescriptions
Criminals use your SSN to access healthcare, fill prescriptions, and receive treatment, creating fraudulent medical records attached to your identity. Medical debts and errors become part of your permanent health record, potentially affecting your insurance eligibility and coverage. Medical identity theft is harder to detect than financial fraud because you may not receive bills or statements immediately.
Request copies of medical records from providers to verify accuracy and identify any services you did not receive. Contact your healthcare providers directly to report the fraud and request that they flag your account for suspicious activity. These three exploitation methods-credit fraud, tax fraud, and medical identity theft-represent the primary ways criminals weaponize stolen SSNs, but detection requires vigilance across multiple fronts.
Spotting Identity Theft Before It Spirals: Serving South Carolina, including Greenville, Columbia and Charleston
The moment criminals open accounts or file returns using your SSN, a clock starts ticking. You have days or weeks before fraudulent activity becomes obvious, but most people miss the early warning signs entirely. The Federal Trade Commission found that identity theft victims typically discover the fraud only after receiving collection notices or spotting credit report damage. Waiting for obvious red flags means you’ve already lost ground-the damage compounds while you remain unaware. Acting on subtle indicators catches fraud at its earliest stage, before criminals drain accounts or destroy your credit score.
Unexpected Bills and Collection Notices
Unexpected bills arriving for accounts you never opened represent one of the clearest signals that someone is using your SSN. These notices come from credit card companies, utility providers, medical offices, or loan servicers offering you accounts you did not request. Many people discard these as junk mail without reading them carefully, but each one signals active fraud.
Check the account number, creditor name, and opening date on every bill that arrives. If you do not recognize the creditor or account, call the company immediately using the phone number on the bill and confirm whether the account exists under your name and SSN. Do not use phone numbers from the bill itself if you suspect fraud-instead, look up the company’s official customer service number independently.
File a dispute with the creditor in writing and request documentation showing how the account was opened. Medical bills deserve particular attention because they often arrive months after services were rendered, giving criminals a significant head start. Request itemized statements showing what services were billed and cross-reference them against your actual medical visits.
Collection notices compound the problem because collection agencies have already purchased your debt from the original creditor, meaning the fraud has progressed further. Respond to collection notices within 30 days with a dispute letter stating that you did not authorize the account and do not owe the debt. Send the letter certified mail with return receipt requested to create documentation of your complaint.
Credit Report Discrepancies and Unauthorized Accounts
Your credit reports contain the most reliable record of fraudulent activity because they show every account opened in your name, every inquiry made by lenders, and every late payment reported. Pull your free annual credit report from all three bureaus-Equifax, Experian, and TransUnion-at AnnualCreditReport.com and examine them carefully for accounts you do not recognize, inquiries from lenders you never contacted, and negative marks on accounts you manage responsibly.
Look for variations of your name that criminals may have used when opening accounts, address changes you did not authorize, and employment history you never provided. The Social Security Administration Office of Inspector General documented cases where unauthorized direct deposit changes via my Social Security redirected about $33.5 million in benefits before SSA prevented roughly $23.9 million in misdirected payments. This happened because victims did not monitor their accounts regularly.
Set a calendar reminder to review your credit reports quarterly rather than waiting for your annual pull, since fraud can surface within weeks. Contact each bureau immediately if you spot discrepancies and request written documentation of any accounts you dispute. Place a fraud alert on your credit file with all three bureaus if you discover unauthorized accounts-this alert flags your file for lenders and forces them to verify your identity before opening new accounts in your name.
Missing Tax Refunds and Suspicious IRS Correspondence
Missing tax refunds or receiving IRS correspondence about filings you did not submit signals that someone filed a return using your SSN. The IRS processes returns electronically and issues refunds within 21 days under normal circumstances, so if your refund arrives late or never arrives, contact the IRS at 1-800-908-4490 immediately.
Request a tax account transcript from the IRS to see all returns filed under your SSN for the current and prior years. If you spot returns you did not file, the IRS will investigate and issue a corrected refund to you rather than the criminal. Do not file your legitimate return until you’ve confirmed that no fraudulent return exists, because filing over a fraudulent return triggers an audit that delays your refund further.
The IRS has procedures specifically designed to handle identity theft cases, so contact them before taking any other action. Suspicious IRS correspondence-notices of wage garnishment, liens, or tax balances you do not owe-indicates that criminals may have filed returns claiming refundable credits or inflated deductions. These notices arrive months after the fraudulent filing because the IRS processes millions of returns before identifying duplicates or inconsistencies.
File an Identity Theft Report with the Federal Trade Commission at IdentityTheft.gov to create an official record that protects you during IRS investigations. This report gives you legal standing to dispute the fraudulent return and guides your recovery steps across all agencies.
Final Steps to Protect Yourself
Start monitoring your credit reports today rather than waiting for a problem to surface. Pull your free annual report from AnnualCreditReport.com and review all three bureaus for accounts you do not recognize. Set a calendar reminder to check your reports every three months instead of annually, since criminals can open accounts and file fraudulent returns within weeks. The Social Security Administration Office of Inspector General found that unauthorized direct deposit changes redirected millions in benefits before victims caught the fraud through regular account monitoring.
Place a fraud alert on your credit file immediately if you discover any suspicious activity. Contact one of the three credit bureaus and request the alert, which forces lenders to verify your identity before opening new accounts in your name. If you’ve already experienced identity theft or believe your SSN has been compromised, request a credit freeze instead-this blocks lenders from accessing your credit file entirely unless you temporarily lift it. Freezes provide stronger protection than alerts and remain in place until you remove them.
Report identity theft to the Federal Trade Commission at IdentityTheft.gov without delay, and file a report with the Social Security Administration Office of Inspector General at oig.ssa.gov or call 1-800-269-0271 if you suspect SSN misuse. Contact your local law enforcement agency and file a police report, which creates an official record you can provide to creditors and the IRS. If you’re facing significant financial damage or complex recovery steps, contact Hays Cauley, P.C. for guidance on protecting your rights and pursuing damages against those responsible for the theft.


