Identity theft can devastate your finances and credit in ways that take years to repair. When criminals steal your personal information, the damage spreads quickly across bank accounts, credit cards, and loan applications.
We at Hays Cauley, P.C. help South Carolina residents navigate identity theft recovery and reclaim their financial stability. This guide walks you through the immediate steps to take, how to repair your credit, and strategies to prevent it from happening again.
What to Do in the First Hours After Identity Theft
Act Fast to Minimize Damage
Speed matters when identity theft strikes. The first 24 hours after discovering unauthorized activity significantly reduce financial losses. Your immediate actions create a paper trail that protects you legally and stops criminals from causing additional damage.
Contact Your Financial Institutions Immediately
Contact your bank and credit card issuers directly using the phone numbers on your statements-not numbers from emails or websites, which could be fraudulent. Tell them which accounts show suspicious activity and ask them to freeze or close compromised cards immediately. Request written confirmation of these actions and the names of representatives you spoke with. Document everything: dates, times, account numbers affected, and what was said.
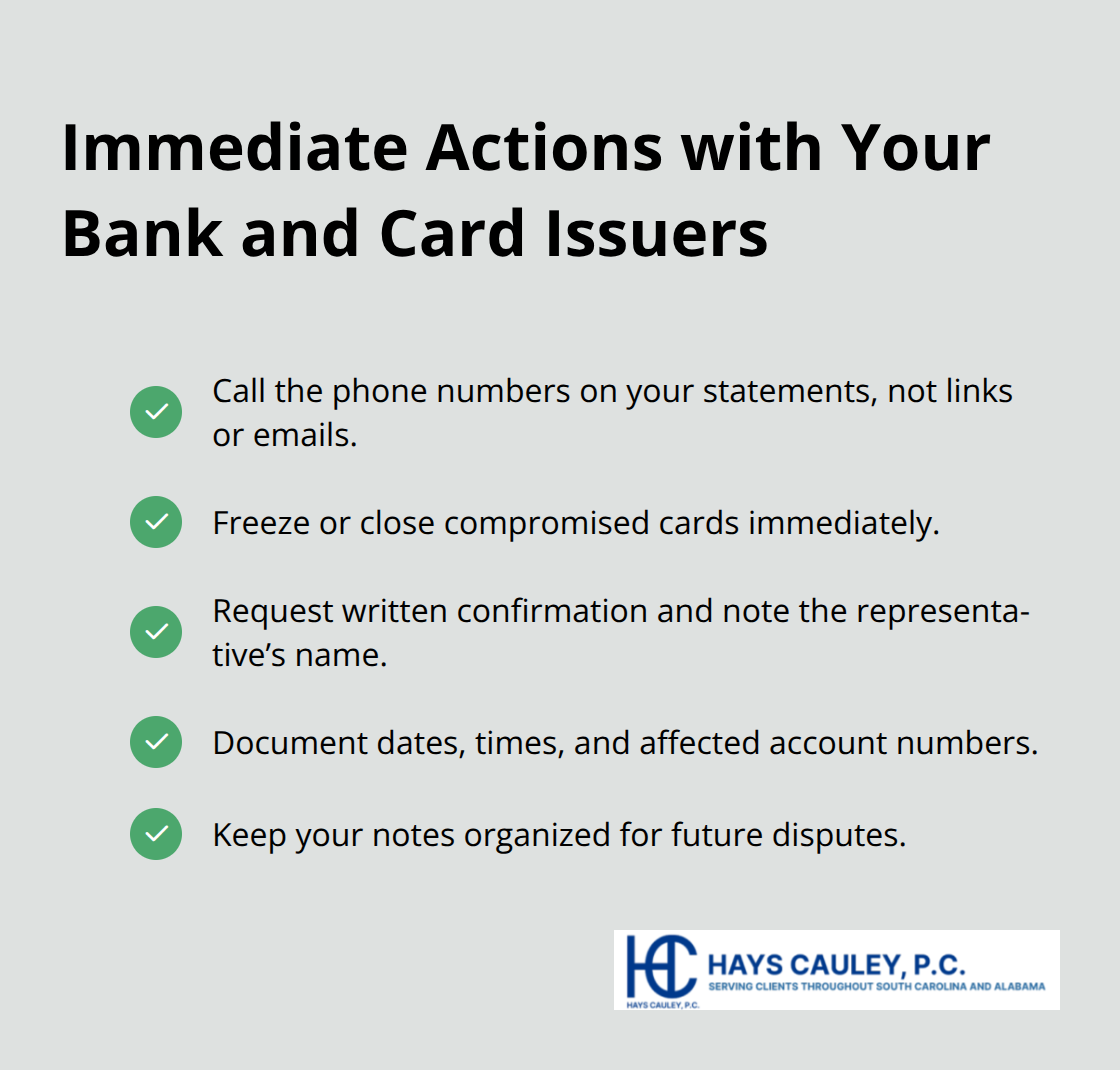
This record becomes critical evidence if disputes arise later.
Alert Credit Bureaus and File Federal Reports
Place a fraud alert with all three credit bureaus simultaneously by calling Equifax, Experian, or TransUnion. The alert lasts one year and tells lenders to verify your identity before opening new accounts-a powerful barrier against fraudsters applying for credit in your name. Then file an official identity theft report through IdentityTheft.gov, which is run by the Federal Trade Commission. This report generates a personalized recovery plan and provides sample letters you can send to creditors and bureaus.
Reach Out to South Carolina Resources
South Carolina residents should also contact the Identity Theft Unit at 800-922-1594 or IDTheftHelp@scconsumer.gov for state-level support and guidance tailored to South Carolina law. The SC Department of Consumer Affairs tracks identity theft patterns and can direct you to resources specific to your situation. These immediate steps-contacting financial institutions, alerting credit bureaus, and filing federal and state reports-establish your status as a victim and create official documentation that strengthens your position when disputing fraudulent charges and accounts.
With your immediate response complete, the next phase involves examining your credit reports in detail to identify all fraudulent activity and begin the repair process.
Rebuild Your Credit After Identity Theft
Pull Your Credit Reports and Spot Fraudulent Activity
Within three to five days of filing your FTC report, pull your credit reports from all three bureaus using AnnualCreditReport.com, the official source for free annual reports. This timing matters because fraudsters often open accounts or make charges within hours of stealing your identity. When you review the reports, look for accounts you never opened, credit inquiries you didn’t authorize, and addresses that aren’t yours. The Bureau of Justice Statistics found that unauthorized use of existing accounts is the most common form of identity theft, followed by opening new accounts in your name. Your reports will show both types of fraud clearly. Write down every fraudulent entry with the account number, the amount, and the date it appeared. This list becomes your roadmap for disputing false information.
File Written Disputes with Credit Bureaus and Creditors
Dispute each fraudulent entry in writing with the credit bureau that reported it, referencing your FTC report number in every letter. Send disputes via certified mail so you have proof of delivery. The bureau must reinvestigate within 30 days under South Carolina Code 37-20-170 and provide you with a revised report if the information is inaccurate. Simultaneously, contact the creditor or lender directly and request written confirmation that the fraudulent account is closed and will be removed from your credit file.
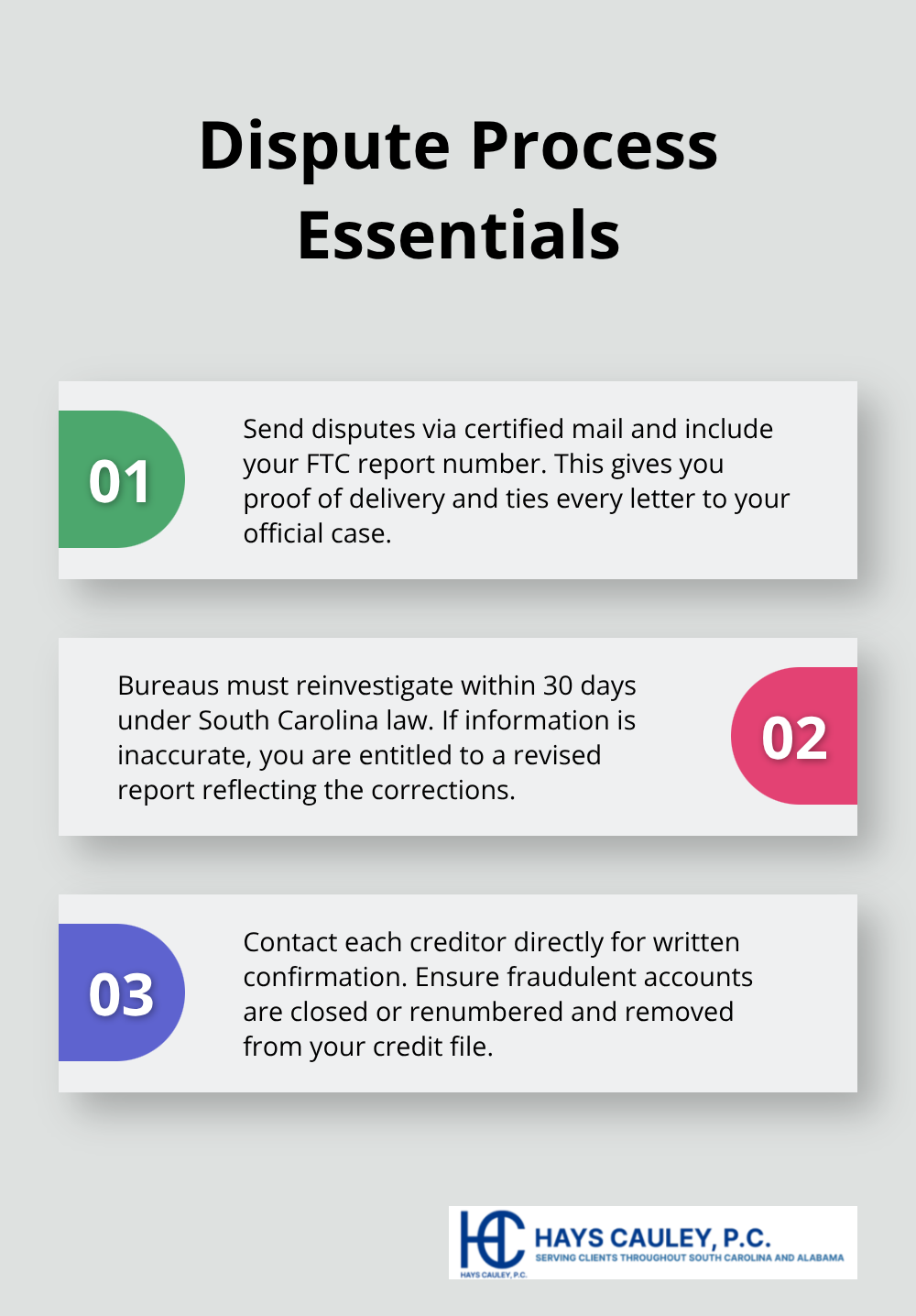
If an account shows fraudulent charges rather than being entirely fake, ask the creditor to issue a new account number and transfer legitimate charges.
Monitor Progress and File Follow-Up Disputes
After disputes are filed, recheck your reports in about 60 days. If fraudulent items remain, file a second dispute with additional documentation and keep a detailed log of every action. South Carolina law allows damages up to three times actual losses or $1,000 per incident if violations are willful, or actual damages or $1,000 per incident for negligent violations. After initial recovery, check your credit quarterly on a rotating schedule, pulling one report every four months from each bureau, and review tax accounts annually.
Secure Your Credit with a Freeze
Place a security freeze on your file at no cost under South Carolina Code 37-20-160, which blocks access to your credit report and prevents new fraudulent accounts entirely. Removing the freeze takes as little as three business days when properly identified. This protection works alongside your monitoring efforts and creates a strong barrier against future fraud attempts. With your credit reports cleaned up and your file secured, the next step involves strengthening your digital defenses to prevent criminals from stealing your information again.
Fortify Your Digital Defenses – Serving South Carolina, including Greenville, Columbia and Charleston
Create Strong Passwords That Stop Criminals
Your passwords form the front line of defense against criminals trying to access your accounts after identity theft recovery. Weak or reused passwords across multiple sites create entry points that attackers exploit relentlessly. Try 16-character passwords for every account, combining uppercase letters, numbers, and symbols in ways that have no connection to personal information like birthdays or pet names. A password manager like Bitwarden or 1Password generates and stores these complex passwords securely, eliminating the temptation to reuse simple variations across accounts. After completing identity theft recovery, update every password on your critical accounts and check each one for remaining vulnerabilities or suspicious activity that might indicate ongoing unauthorized access.
Activate Two-Factor Authentication on Financial Accounts
Two-factor authentication adds a second verification step that stops unauthorized access even if criminals obtain your password. Use authenticator apps like Google Authenticator or Microsoft Authenticator instead of SMS text messages, which hackers can intercept through SIM swapping. Enable this protection on all financial accounts and email addresses immediately after recovery. This dual-layer approach makes account takeover significantly harder for fraudsters to accomplish.
Secure Your Mobile Devices
Mobile devices hold sensitive financial apps and email access, making them targets for criminals. Turn on automatic lock after five minutes of inactivity and protect your phone with a strong PIN or biometric authentication. Access your accounts on secure home networks rather than public WiFi, which criminals can monitor to capture login credentials. These steps prevent attackers from gaining physical or wireless access to your financial information.
Monitor Accounts and Set Up Recurring Reviews
Continuous monitoring transforms recovery into long-term security practices that guard against repeat victimization. Pull rotating free credit reports from AnnualCreditReport.com every four months and set calendar reminders to review tax accounts annually for fraudulent returns or W-2 fraud. The SC Department of Consumer Affairs Identity Theft Unit at 800-922-1594 can answer questions about ongoing protection strategies tailored to South Carolina residents.
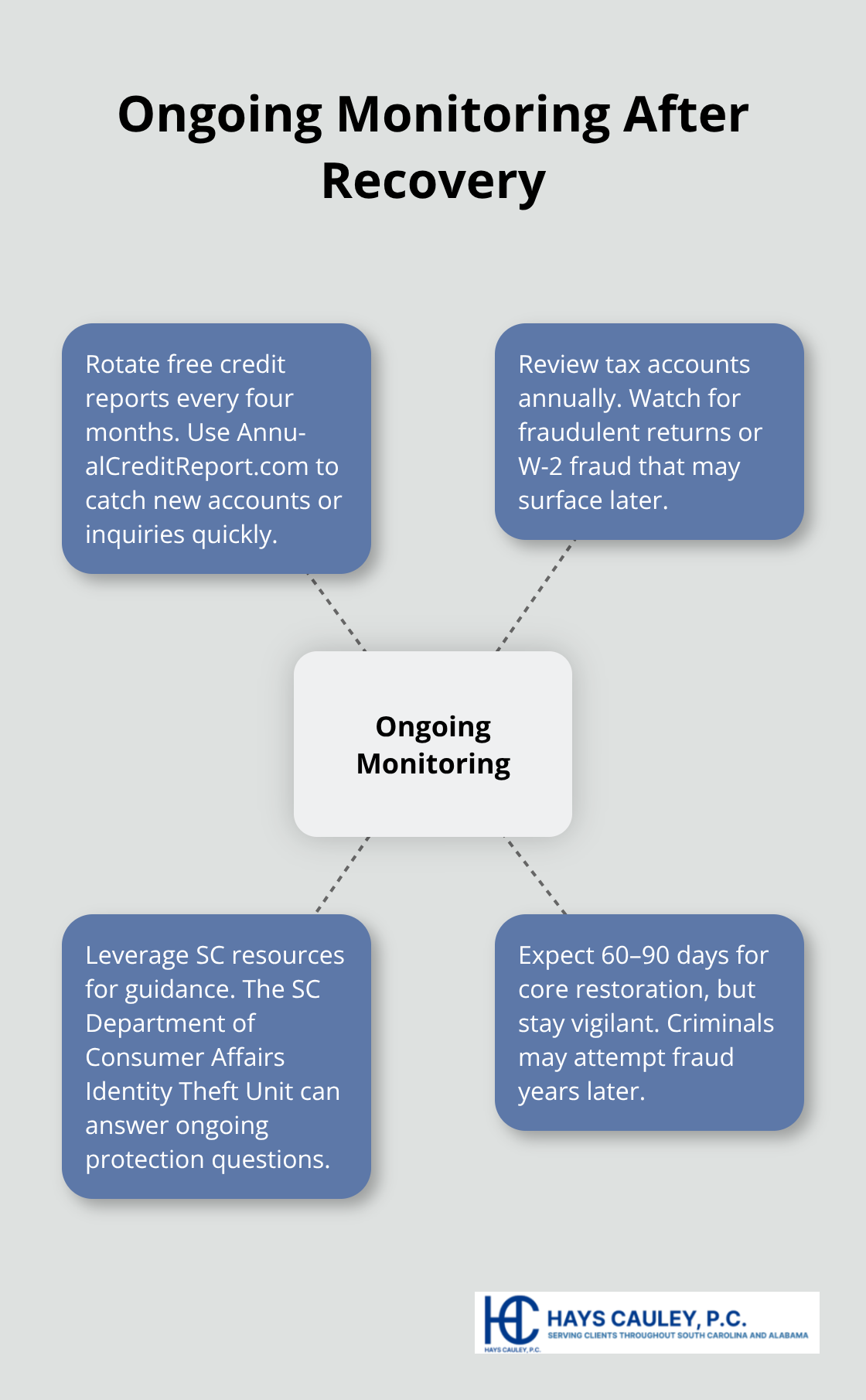
Identity theft recovery typically spans 60 to 90 days for core restoration, but vigilance remains necessary indefinitely because criminals sometimes attempt fraud years after the initial theft.
Final Thoughts
Identity theft recovery in SC unfolds over weeks to months, with most victims completing core restoration within 60 to 90 days. Your immediate actions in those first 24 hours-contacting financial institutions, placing fraud alerts, and filing FTC and state reports-establish the foundation for everything that follows. The repair phase takes longer because credit bureaus have 30 days to investigate disputes, and some creditors move slowly on account closures.
Some identity theft cases involve complications that benefit from professional guidance. If criminals opened accounts in your name and those accounts went to collections, if fraudulent tax returns were filed, or if your identity was used to commit crimes, navigating the legal and financial fallout becomes significantly more complex. We at Hays Cauley, P.C. help South Carolina residents resolve these difficult situations by handling disputes with creditors, working with credit bureaus, and addressing legal issues that arise from identity theft.
South Carolina residents have access to multiple resources throughout recovery, including the SC Department of Consumer Affairs Identity Theft Unit at 800-922-1594 or IDTheftHelp@scconsumer.gov, the FTC’s IdentityTheft.gov site, and AnnualCreditReport.com for free credit reports. If your situation involves legal disputes, debt collection issues, or complex credit reporting problems, Hays Cauley, P.C. can provide the consumer protection support you need to restore your financial life.