Identity theft costs Americans over $20 billion annually, and criminals are getting smarter about hiding their tracks. At Hays Cauley, P.C., we help clients understand the red flag rules for identity theft that can stop fraud before it starts.
Knowing what to look for makes all the difference. This guide walks you through the warning signs, legal requirements, and practical steps to protect yourself and your business.
What Red Flag Rules Are and Why They Matter
The Red Flags Rule is a federal requirement under the Fair Credit Reporting Act that mandates financial institutions and creditors implement a written Identity Theft Prevention Program. This program must identify, detect, and respond to warning signs of identity theft in daily operations. The rule applies broadly to banks, credit unions, savings and loan associations, and any organization offering covered accounts-which means accounts used for personal, family, or household purposes that involve multiple payments or transactions. Nine million Americans experience identity theft annually according to FTC data, making this regulation essential rather than optional.
Understanding Covered Accounts and Risk Assessment
Financial institutions must conduct risk assessments to determine which accounts qualify as covered. These assessments examine how accounts are opened, how customers access them, and past experiences with identity theft. Once an organization identifies covered accounts, it establishes policies that address five core categories of red flags: alerts from credit reporting agencies, suspicious documents, inconsistencies in personal identifying information, unusual account activity, and warnings from customers or law enforcement. The program requires board or senior management oversight, staff training, and regular updates as fraud methods evolve.
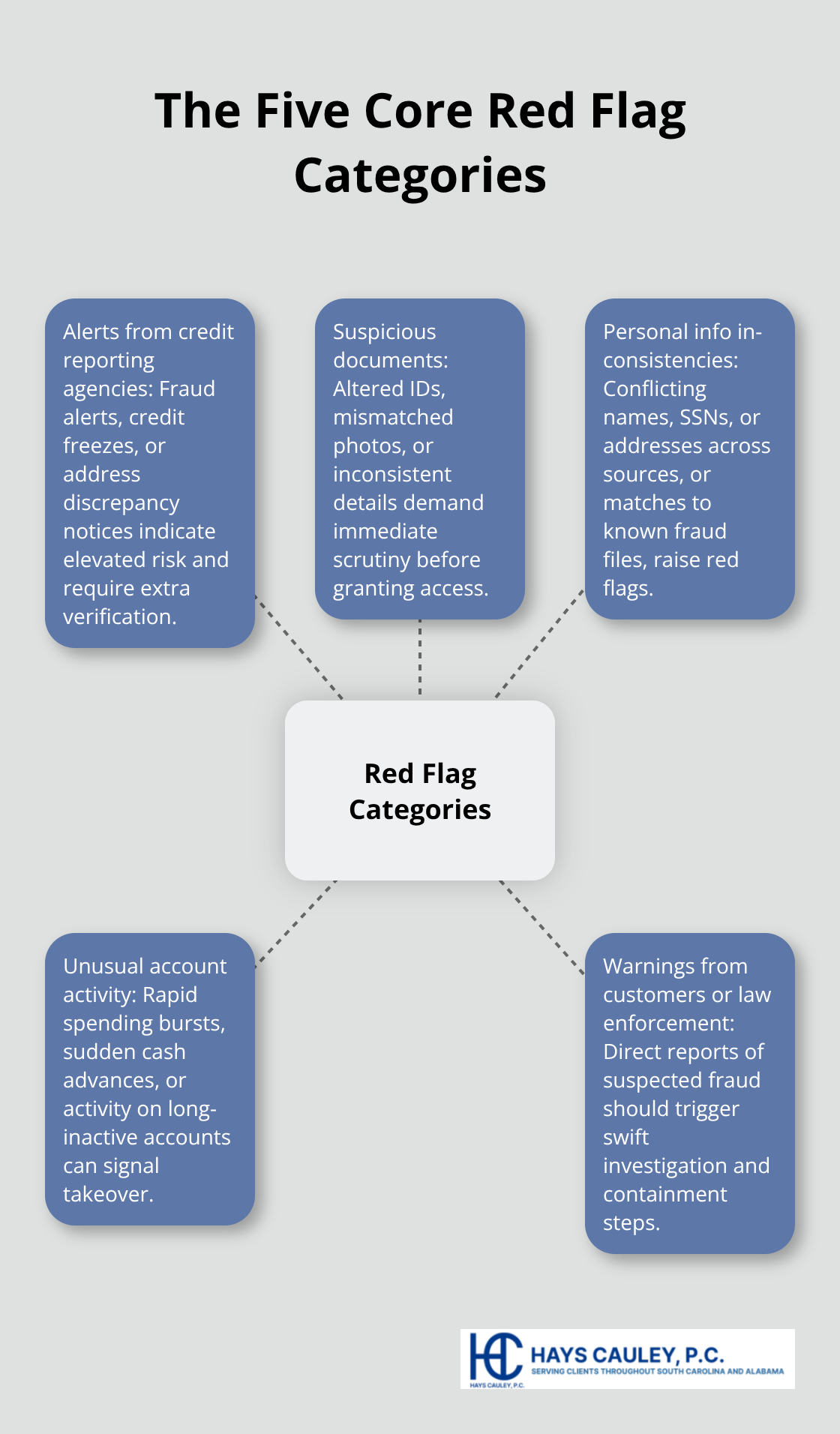
The Five Core Red Flag Categories
Organizations monitor alerts from credit reporting agencies, including fraud alerts and credit freezes that signal heightened risk. Suspicious documents-altered IDs, mismatched photos, or inconsistent information-trigger immediate investigation. Personal identifying information that conflicts across sources or matches known fraud cases raises concerns. Unusual account activity, such as rapid spending patterns or inactive accounts suddenly becoming active, demands attention. Warnings from customers, law enforcement, or identity theft victims prompt swift action to prevent further damage.
Concrete Warning Signs in Daily Operations
Red flags are concrete warning signs, not abstract concepts. When a customer’s address changes and a replacement card is requested within 30 days, that requires verification. When someone provides identification that doesn’t match their appearance or contains information inconsistent with previous submissions, that is actionable. When credit inquiries spike or new accounts appear in rapid succession, that signals potential fraud. The FTC’s Appendix A lists 26 specific red flags that organizations should monitor, including situations where the same social security number appears on multiple applications, where available credit is suddenly used for cash advances or high-value items with no first payment made, or where account statements are returned as undeliverable despite ongoing transactions.
Why Detection Prevents Losses
Detecting these patterns prevents losses before they occur. Businesses avoid unpaid bills and reputational damage, while consumers avoid drained bank accounts and damaged credit. Organizations that fail to implement adequate programs face enforcement action from the FTC, which actively monitors compliance across the financial services industry. Understanding these warning signs allows you to take protective action in your own accounts and recognize when fraud may be occurring.
Red Flags That Appear in Your Accounts and Documents
Unauthorized Transactions and Account Changes
Identity theft red flags appear in specific, measurable patterns within your accounts and documents. When your credit card or bank statement shows transactions you didn’t authorize, that signals immediate fraud. But the fraud often starts earlier, in patterns most people miss. A change of address request followed by a request for a replacement card within 30 days represents a concrete red flag the FTC identifies-criminals typically change the mailing address first to intercept statements. If you receive a credit freeze notice from a credit bureau you didn’t request, someone else attempted to open an account in your name. Unusual spending patterns matter equally. If your account suddenly shows cash advances, jewelry purchases, or electronics buys when you normally make modest purchases, that signals fraud. The FTC notes that accounts inactive for months that suddenly spike with activity are classic indicators of identity theft.
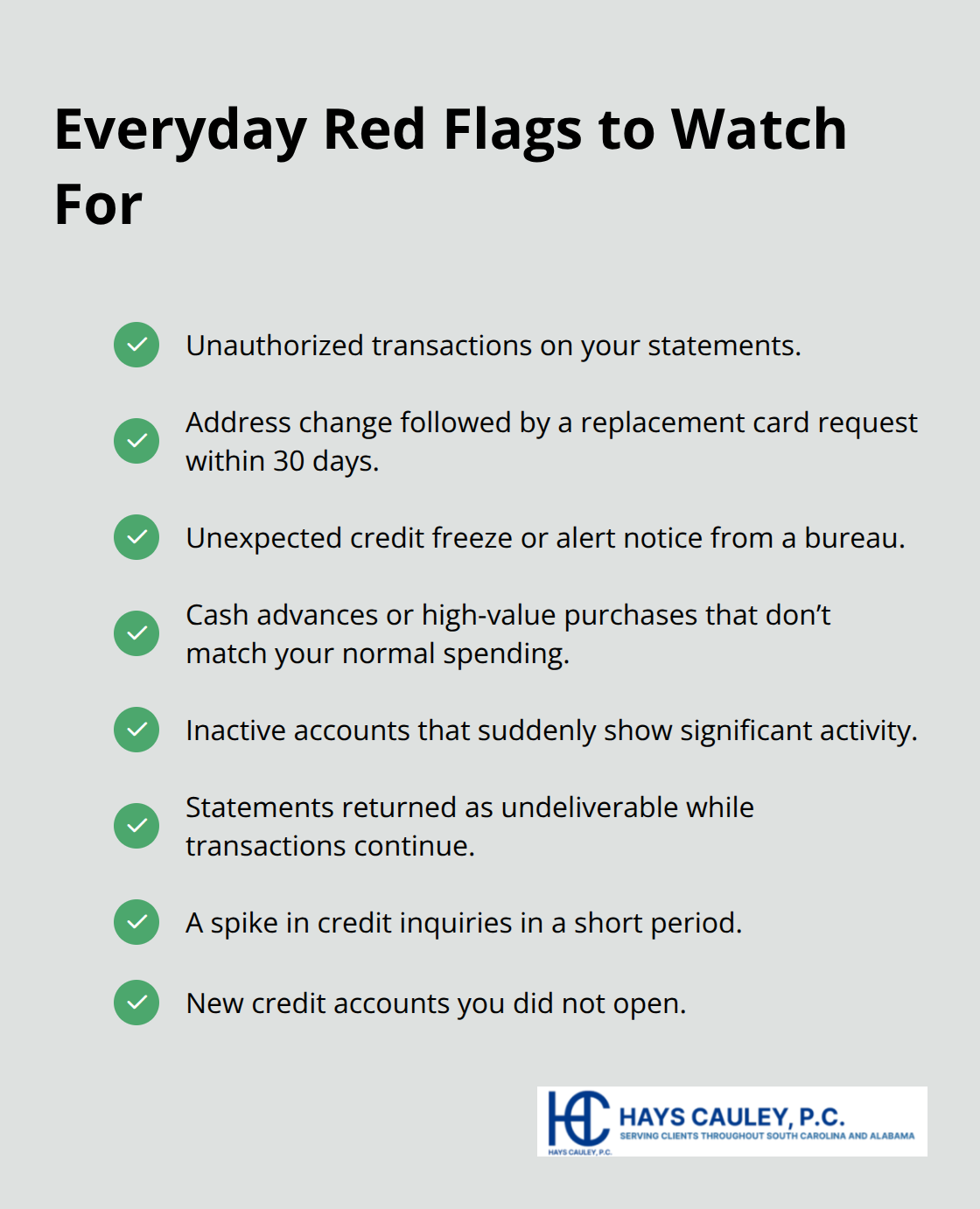
Document Discrepancies and Personal Information Mismatches
Document discrepancies reveal fraud attempts before accounts fully activate. When identification documents don’t match your appearance, contain information inconsistent with what you provided, or show signs of alteration, those are actionable warning signs. Social security number mismatches across applications-where the same SSN appears on multiple accounts you didn’t open-represent a critical red flag. Addresses linked to prisons, answering services, or PO boxes on applications should trigger immediate suspicion. These details matter because fraudsters often use inconsistent information to avoid detection, and inconsistencies expose their schemes.
Credit Inquiries and New Account Openings
Credit inquiries and new account openings reveal identity theft most visibly to you. A significant jump in credit inquiries within a short period indicates someone is applying for accounts in your name. New credit accounts appearing on your credit report that you didn’t authorize demand immediate investigation. The FTC data shows that rapid-fire account openings represent among the fastest ways fraudsters drain available credit. If statements are returned as undeliverable despite active transactions on your account, that reflects a deliberate attempt to hide fraud from you. Address discrepancy notices from credit bureaus warrant serious attention because they often precede fraudulent account openings.
Taking Immediate Action
When you notice these patterns, contact your bank or credit card issuer immediately and place a credit freeze with major bureaus-this prevents new accounts from being opened in your name. The faster you identify these warning signs, the faster you can address the damage. These detection steps form the foundation of your personal defense, but organizations and businesses face additional obligations to monitor and respond to red flags on a systematic level.
Building an Identity Theft Prevention Program That Actually Works
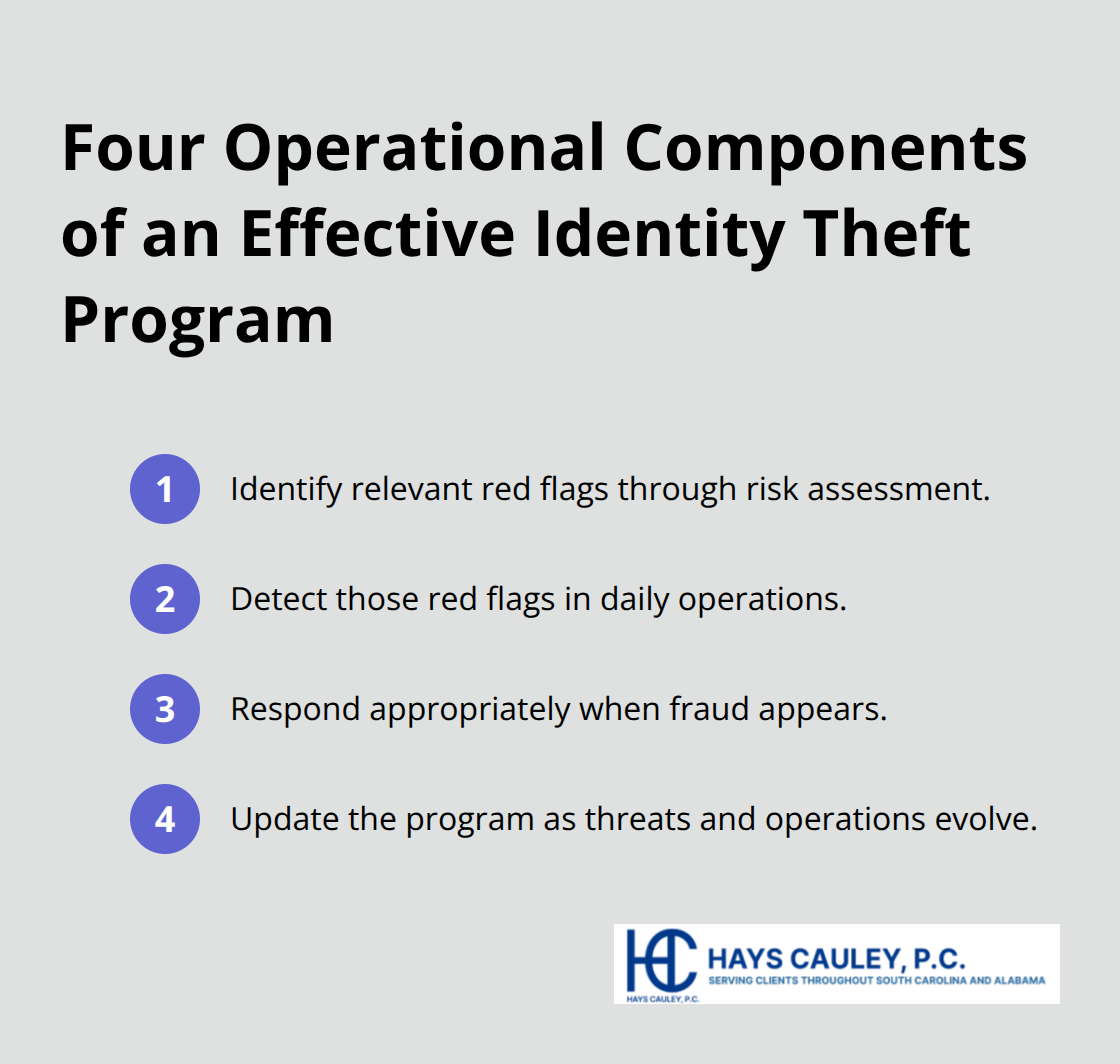
Organizations need more than a document sitting in a drawer. The FTC requires a written Identity Theft Prevention Program with four operational components: identify red flags through risk assessment, detect those red flags in daily operations, respond appropriately when fraud appears, and update the program as threats evolve. This means board or senior management must approve the program, staff must receive training, and service providers need oversight.
Conduct a Risk Assessment Tailored to Your Operations
Start with a genuine risk assessment of your covered accounts. Examine how accounts open, how customers access them, and your organization’s history with identity theft incidents. This assessment determines which of the 26 specific red flags from the FTC’s Appendix A apply to your business. A community bank faces different risks than an online retailer, so your program must reflect your actual operations.
Document Policies and Procedures in Writing
Document everything. Write policies that specify which red flags your organization monitors, how staff will detect them, and what happens when someone identifies suspicious activity. Include concrete procedures for address changes, document verification, and unusual transaction patterns (such as rapid spending on inactive accounts or cash advances on newly opened lines of credit).
Many organizations fail compliance not because they lack good intentions but because they never committed their processes to writing or failed to train staff on what they created.
Train Staff to Recognize and Report Red Flags
Staff training separates effective programs from ineffective ones. Your employees must recognize the 26 specific red flags and know exactly what to do when they spot one. Train them on altered identification documents, mismatched photos on IDs, social security numbers appearing on multiple applications, and sudden spending spikes on inactive accounts. When a customer’s address changes and a replacement card is requested within 30 days, staff should verify the change before issuing the card. Make this training mandatory and recurring because fraud methods change constantly.
Establish Clear Response Procedures and Documentation
Response procedures must be specific and actionable. When someone detects a red flag, define who gets notified, what investigation steps occur, and when law enforcement involvement is appropriate. Options include monitoring the account more closely, contacting the customer to verify activity, changing passwords or security codes, closing the account, or notifying law enforcement. Document every red flag you detect and every action you take. This documentation demonstrates compliance to the FTC and protects your organization during audits (which carry enforcement consequences for non-compliance).
Update Your Program as Threats and Operations Change
Update your program annually at minimum, or whenever your business changes through mergers, acquisitions, new service providers, or new account types. Organizations that implement these systematic approaches reduce identity theft losses significantly while meeting FTC requirements.
Final Thoughts
Red flag rules for identity theft protect you only when you act on the warning signs you spot. Address changes followed by card requests, unauthorized transactions, sudden credit inquiries, and mismatched documents all signal fraud in progress. Contact your bank or credit card issuer immediately if you notice these patterns, place a credit freeze with the three major credit bureaus, and file a report with the FTC at IdentityTheft.gov to create an official record.
Organizations that implement systematic detection and response procedures reduce losses significantly while meeting FTC requirements. Staff training on the 26 specific red flags, written policies for address verification and transaction monitoring, and documented responses to suspicious activity separate compliant programs from ineffective ones. Update your program annually or whenever your business changes through mergers, acquisitions, or new service providers.
At Hays Cauley, P.C., we help consumers navigate identity theft, credit reporting disputes, and debt-related issues throughout South Carolina, including Greenville, Columbia, and Charleston. If fraudulent accounts, damaged credit, or creditors pursuing debts you didn’t incur are affecting your financial standing, we understand the complexity involved and work to protect your rights. Contact us to learn how we can help you address identity theft and restore your financial security.


