Your personal information is valuable to criminals operating on the dark web. Data breaches expose millions of records yearly, and thieves use stolen details to commit fraud and identity theft.
Dark web monitoring helps you detect when your information appears in criminal marketplaces before serious damage occurs. We at Hays Cauley, P.C. created this guide to show you how monitoring works and what steps protect your identity.
How Your Data Reaches Criminal Marketplaces – Serving South Carolina, including Greenville, Columbia and Charleston
Criminals don’t steal your information all at once from a single source. Data reaches the dark web through multiple pathways, each creating a different risk window. According to the FBI Internet Crime Complaint Center, credential stuffing remains one of the most common attack vectors linked to leaked credentials from the dark web. When a breach exposes your email and password, attackers immediately test those credentials across banking sites, email accounts, and social media platforms.
The Credential Reuse Problem
A single compromised password can unlock access to dozens of accounts if you’ve reused it across services. The dark web operates continuously with a global market ecosystem where criminals trade stolen data in real time. Names, addresses, phone numbers, Social Security numbers, emails, usernames, passwords, medical records, financial account numbers, and identity documents all sell on these hidden marketplaces. Full identity packages, known as fullz data, typically sell for around $30 according to CrowdStrike’s threat research.
How Criminals Obtain Your Data
Phishing attacks remain a primary entry point-criminals send urgent-sounding emails requesting account verification or claiming suspicious activity, then harvest your credentials when you respond. Malware and keylogging software installed through malicious downloads or compromised websites silently capture everything you type, including passwords and financial information. Insecure networks, particularly public Wi-Fi without encryption, allow attackers to intercept your data as it travels between your device and websites. Vulnerabilities in software go unpatched for months, giving criminals time to exploit them before companies release fixes.
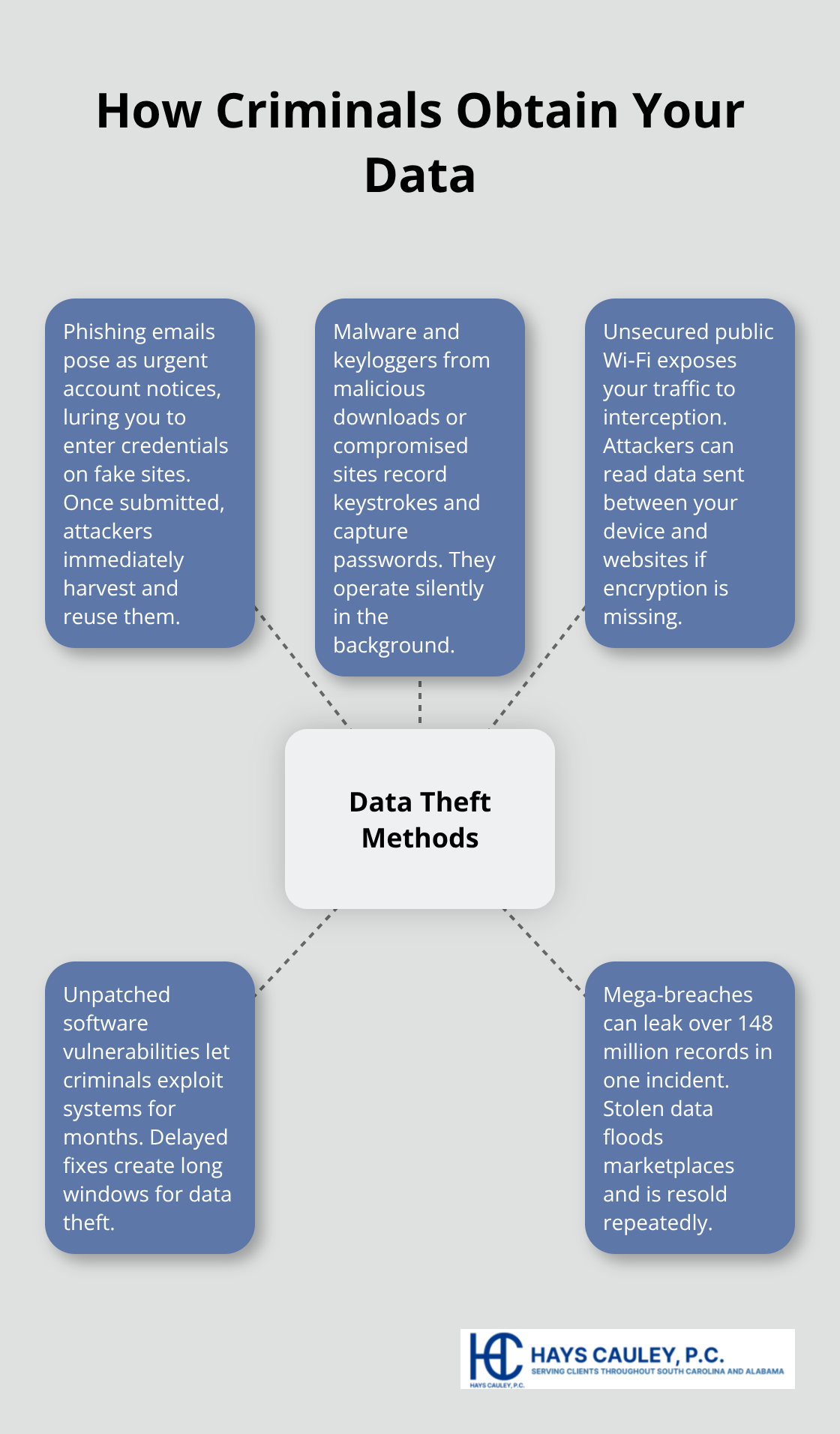
The scale of these breaches is staggering-some incidents involve over 148 million records stolen in a single attack, meaning your data could be among millions offered for sale simultaneously.
What Happens When Your Data Sells
Once your information appears on the dark web, criminals immediately weaponize it. The FBI IC3 and Europol data show that attackers use stolen credentials for credential stuffing attacks, attempting to access your legitimate accounts before you even know you’ve been compromised. With your Social Security number and personal details, criminals open new credit accounts in your name, apply for loans, or take out lines of credit they have no intention of paying back. Medical fraud becomes possible when attackers use your identity to obtain prescriptions or claim insurance benefits. Fraudulent tax returns filed in your name can delay your legitimate refunds by months while the IRS investigates. Government benefits claimed using your information create complex problems requiring coordination with multiple agencies to resolve.
The Ongoing Threat of Lingering Data
Data lingers on the dark web long after initial exposure-the FTC emphasizes that ongoing monitoring remains essential rather than a one-time check. A dark web scan looking back to 2006 across more than 600,000 pages can reveal where your data was exposed and guide your next steps. The sooner you detect your information on the dark web, the narrower the window criminals have to cause financial damage. This is why dark web monitoring paired with immediate action matters far more than hoping your information never surfaces. Understanding these threats makes the case for proactive detection tools that alert you the moment your information appears in criminal marketplaces.
What to Look for in Dark Web Monitoring Services
How Dark Web Monitoring Works
Dark web monitoring services scan hidden marketplaces and forums continuously to detect when your personal data appears in criminal databases. The process differs fundamentally from traditional antivirus software or credit monitoring alone. These services maintain access to dark web databases and use specialized tools to search for your Social Security number, email addresses, phone numbers, usernames, passwords, and financial account details across criminal forums and marketplaces.
When they find a match, they send alerts that allow you to act before criminals weaponize your information.
Speed and Scope of Detection
The speed of detection matters enormously. Services offering near-real-time alerts across multiple data types catch compromises faster than quarterly credit report reviews. Look for monitoring that covers bank accounts and property titles specifically, since these represent high-value targets for criminals. The scope of coverage varies significantly between providers-some services scan only a few thousand websites, while comprehensive platforms monitor more than 600,000 pages and track data dating back to 2006. This historical depth reveals where your information was exposed and helps you understand which accounts need immediate attention.
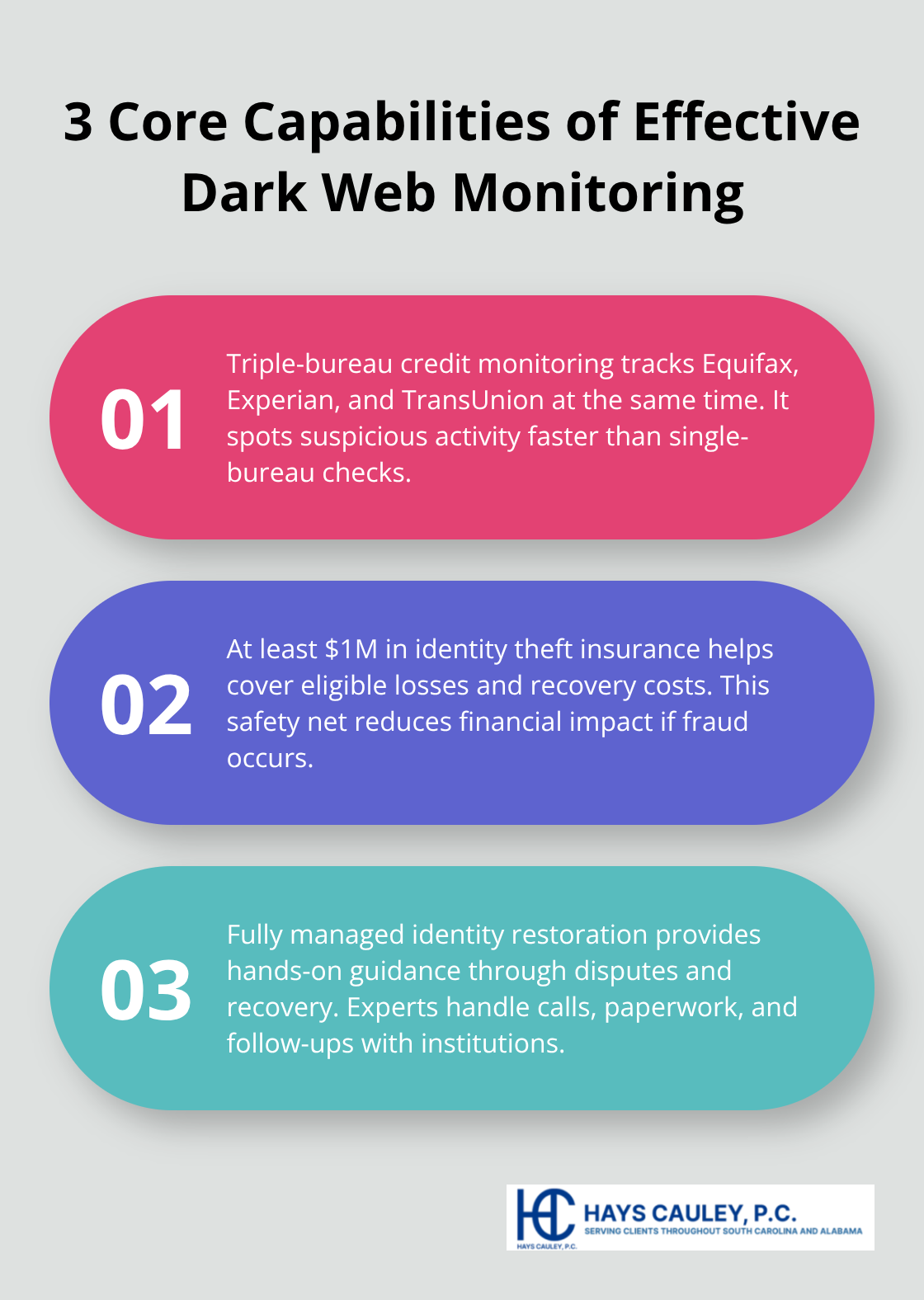
Core Capabilities That Matter
The most effective dark web monitoring combines three core capabilities that work together. First, triple-bureau credit monitoring tracks activity across Equifax, Experian, and TransUnion simultaneously, catching suspicious credit actions faster than single-bureau services. Second, the service should include identity theft insurance of at least one million dollars, providing financial protection if fraud occurs despite your vigilance. Third, look for fully managed identity restoration services where the provider guides you through recovery steps rather than leaving you to navigate the process alone.
Pricing and Feature Comparison
Pricing typically ranges from $7.50 to $30 monthly depending on coverage scope and family size, with annual plans offering significant discounts. Individual plans start around $12 monthly, while family plans covering multiple adults and dependents cost approximately $30 monthly. The features justifying these costs include real-time alerts from all three credit bureaus, monthly or quarterly credit reports from each bureau, and automated dark web scans running continuously. Services that bundle dark web monitoring with VPN protection and antivirus software reduce your overall cost while strengthening your defense by preventing data theft before it reaches criminal marketplaces.
Distinguishing Real Monitoring from Database Checks
When evaluating options, verify that the service actually monitors the dark web rather than simply checking if your information appears in known breach databases, since these represent fundamentally different capabilities. A service that searches only existing breach records misses new data dumps, forum posts, and marketplace listings that emerge daily. Real dark web monitoring requires continuous scanning of hidden sites and marketplaces where criminals actively trade stolen information. This distinction determines whether you receive alerts about threats that matter or outdated information about breaches you already know about. Understanding these differences helps you choose a service that actually protects you rather than one that simply checks boxes on a feature list.
Acting Fast When Your Data Appears on the Dark Web – Serving South Carolina, including Greenville, Columbia and Charleston
Immediate Password and Account Security Actions
The moment a dark web monitoring service alerts you that your information has been compromised, speed determines whether you suffer minor inconvenience or major financial damage. If your Social Security number, financial account details, or login credentials appear in criminal marketplaces, change passwords immediately on every account where you’ve used the same or similar credentials. The FTC emphasizes that this action must happen within hours, not days, because credential stuffing attacks begin the moment criminals obtain your information. Enable multi-factor authentication on all accounts that support it, preferring authenticator apps or hardware keys over SMS-based codes according to NIST guidelines, since text messages can be intercepted through SIM swapping attacks.
Contact your banks and credit card issuers directly using phone numbers from their official websites, never using contact information from emails or texts, and request they flag your accounts for fraud monitoring. If financial account numbers were exposed, ask your institutions whether you need new account numbers entirely, as some breaches require complete account replacements rather than simple monitoring.
Protecting Your Social Security Number and Credit Files
For your Social Security number specifically, contact the Social Security Administration and the IRS directly to alert them of potential misuse, then place a fraud alert on your credit files with all three bureaus simultaneously. This action prevents criminals from opening new accounts in your name for at least one year. The FTC provides free annual credit reports through AnnualCreditReport.gov, and you should pull reports from all three bureaus within days of discovering your data on the dark web, looking specifically for accounts you didn’t open and inquiries you didn’t authorize.
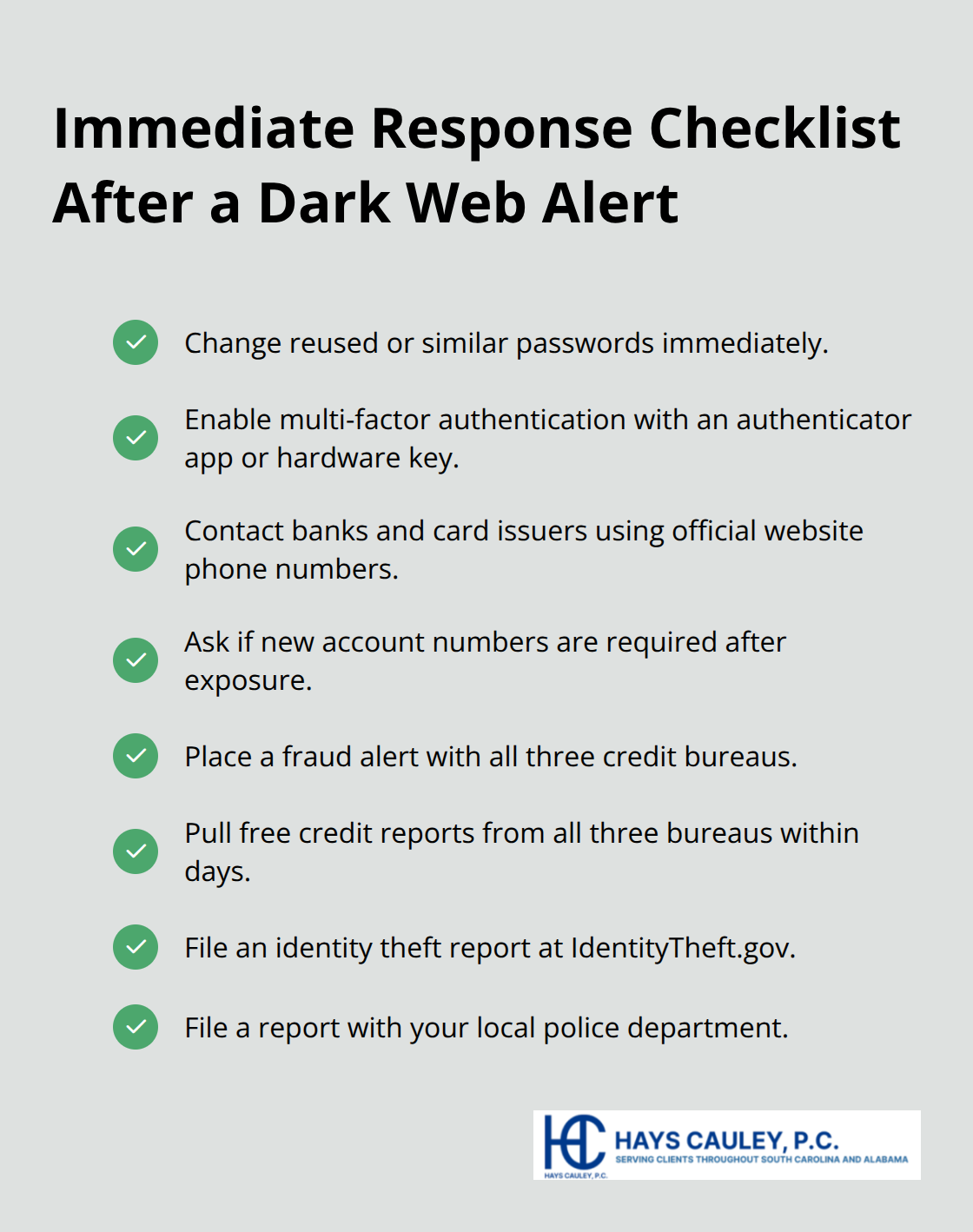
Ongoing Monitoring and Documentation
Review your credit reports for the next several months in addition to these initial checks, since some criminals wait weeks or months before weaponizing stolen information, allowing time for fraudulent accounts to appear. Contact the Federal Trade Commission at IdentityTheft.gov to file an official identity theft report, which creates a record that law enforcement and financial institutions recognize. File a report with your local police department as well, obtaining a case number that strengthens your credibility when disputing fraudulent accounts.
Getting Professional Support for Recovery
If you discover actual fraud rather than just exposed data, the Identity Theft Resource Center offers free assistance to victims navigating recovery steps tailored to your specific situation. Document everything meticulously including dates you discovered the breach, companies you notified, case numbers from law enforcement, and correspondence with financial institutions, since this documentation supports your claims when disputing fraudulent accounts and proves you acted responsibly. If fraudulent accounts cause significant damage or if creditors pursue you for accounts opened in your name without authorization, Hays Cauley, P.C. can guide you through legal options available to you.
Final Thoughts
Dark web monitoring reveals a hard truth: your personal information has value to criminals, and waiting passively for trouble guarantees you’ll discover compromises too late. The threats are real and measurable-criminals trade stolen data continuously across global marketplaces, full identity packages sell for around $30, and breaches routinely expose millions of records simultaneously. Your Social Security number, financial account details, and login credentials represent immediate targets for credential stuffing, fraudulent account openings, and identity theft that can take months to resolve.
Implement dark web monitoring as part of your defense strategy, selecting a service that scans continuously across more than 600,000 pages and provides near-real-time alerts when your information surfaces. Pair this monitoring with triple-bureau credit tracking, strong passwords managed through a password manager, and multi-factor authentication on every account that supports it. These layers work together to catch compromises early and prevent criminals from weaponizing your data before you respond.
When alerts arrive, act immediately-hours matter, not days. Change compromised passwords, contact your financial institutions, place fraud alerts on your credit files, and file reports with the FTC and local law enforcement. If fraud occurs despite your vigilance or if creditors pursue you for accounts opened fraudulently in your name, contact Hays Cauley, P.C. to explore your legal options and navigate credit reporting disputes, identity theft recovery, and debt-related issues that result from compromised information.


